VLANs — Virtual Local Area Networks — are one of the most powerful tools available to network administrators at every scale. A properly configured VLAN architecture divides a single physical network into multiple isolated logical segments, improves security by containing lateral movement between device groups, and gives administrators precise control over which devices communicate with each other.
What Is a VLAN and Why Does It Matter?
A VLAN is a logical network segment created within a managed switch that groups devices together regardless of their physical location. Devices on the same VLAN communicate directly. Devices on different VLANs cannot communicate unless traffic passes through a Layer 3 router or switch that explicitly permits the connection.
This isolation delivers three core benefits. It improves security by preventing a compromised device on one VLAN from reaching devices on another. And it reduces broadcast traffic by keeping broadcasts within their originating VLAN. It enables independent policy enforcement — different firewall rules, QoS settings, and access controls apply to each VLAN separately.
What You Need Before You Start
A Managed Switch: Unmanaged switches do not support VLANs. Choose a managed switch with 802.1Q VLAN support from Cisco, Ubiquiti UniFi, Netgear, TP-Link, or MikroTik.
A VLAN-Capable Router: Your router must support VLAN subinterfaces for inter-VLAN routing. pfSense, OPNsense, Ubiquiti Dream Machine, and most modern business routers handle this natively.
A Clear VLAN Plan: Define each VLAN’s ID number, name, purpose, subnet, and port assignments before touching any configuration. A clear plan prevents errors that disrupt connectivity during setup.
Switch Management Access: Access the switch through its web GUI or CLI using the default IP address printed on the device or listed in its documentation.
Plan Your VLAN Architecture
Define each VLAN with a unique ID between 1 and 4094 and a descriptive name. A practical plan for a home or small business network:
VLAN 1 — Management. Switch and network device administration only. Restrict to authorized administrators.
VLAN 10 — Trusted Devices. Personal computers, laptops, and phones you control fully.
VLAN 20 — Servers and NAS. File servers and network storage accessible to other VLANs selectively.
VLAN 30 — IoT Devices. Smart home sensors, cameras, and smart speakers isolated from trusted devices.
VLAN 40 — Guest Network. Visitor devices with internet access only — no internal resource access.
VLAN 50 — VoIP. IP phones with dedicated QoS priority and network isolation.
Write this plan down before beginning configuration. Every subsequent step references it directly.
Create VLANs on the Switch
Log into your switch management interface. Navigate to the VLAN configuration section — found under Switching, VLANs, or 802.1Q VLAN depending on your platform.
Create each VLAN by entering its ID number and name. On Cisco CLI, enter global configuration mode and use the vlan command followed by the ID, then the name command to label it. On web GUI platforms like Netgear or TP-Link, click Add VLAN, enter the ID and name, and save. The process takes under two minutes per VLAN.
Assign Ports to VLANs
Every switch port operates in one of two modes.
Access Ports carry traffic for a single VLAN only. Connect end devices — computers, cameras, phones — to access ports. The connected device has no awareness that VLANs exist. Configure access ports by assigning them to their designated VLAN as untagged members.
Trunk Ports carry traffic for multiple VLANs simultaneously by tagging each ethernet frame with its VLAN ID using 802.1Q. Connect trunk ports to other switches, routers, and wireless access points that serve multiple SSIDs across different VLANs. Configure trunk ports as tagged members of every VLAN they need to carry.
A port connecting a laptop assigns to VLAN 10 as untagged. A port connecting a wireless access point configures as a trunk port carrying VLANs 10, 30, and 40 tagged — one per SSID. Assign every port explicitly. Unassigned ports default to VLAN 1 and expose your management network unintentionally.
Configure the Router for Inter-VLAN Routing
Connect the switch uplink to your router using a trunk port carrying all VLANs tagged. On pfSense or OPNsense, create a VLAN subinterface for each VLAN on the physical interface connected to your switch. Assign each subinterface its VLAN ID and a unique gateway IP — VLAN 10 uses 192.168.10.1, VLAN 20 uses 192.168.20.1, VLAN 30 uses 192.168.30.1.
Create firewall rules that define which inter-VLAN traffic you permit. Block all inter-VLAN traffic by default and add specific allow rules only for legitimate communication paths. Allow VLAN 10 trusted devices to reach VLAN 20 servers on specific ports. Block all other inter-VLAN communication by default.
Configure Wireless Access Points for VLAN SSIDs
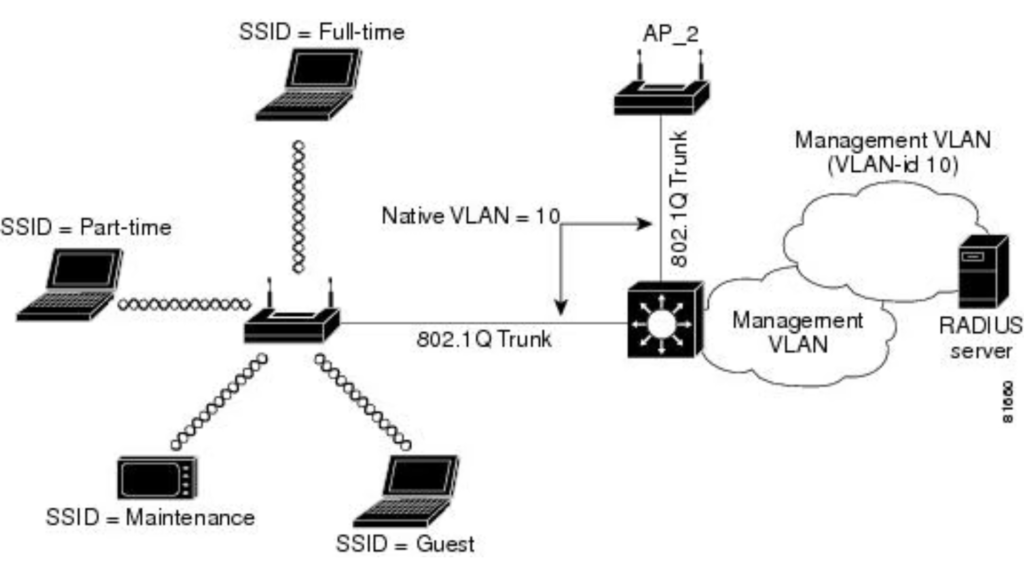
Assign each Wi-Fi SSID to its corresponding VLAN through your access point management interface. Set your trusted SSID to VLAN 10, IoT SSID to VLAN 30, and guest SSID to VLAN 40. When a device connects to the guest SSID, the access point tags its traffic with VLAN 40 before forwarding it to the switch — placing it on the guest VLAN automatically.
Ensure the port connecting each access point to the switch is a trunk port carrying all VLANs that access point serves. A single ethernet cable carries all SSID traffic correctly tagged for each VLAN.
Test and Verify Your VLAN Configuration
Connect a device to each VLAN and verify it receives an IP address in the correct subnet from the DHCP server assigned to that VLAN.
Test inter-VLAN isolation by pinging a device on a different VLAN. Unpermitted traffic should fail — confirming your firewall rules enforce isolation correctly. Test permitted inter-VLAN paths to confirm allow rules function as intended. Verify guest devices reach the internet but cannot reach any internal resource. Confirm IoT devices communicate with cloud services but cannot initiate connections to trusted devices or servers.
Common VLAN Mistakes to Avoid
Forgetting to configure the trunk port between your switch and router correctly prevents all inter-VLAN routing. Leaving devices on VLAN 1 unintentionally exposes your management network. Creating overly permissive inter-VLAN firewall rules defeats the security purpose of segmentation entirely. Skipping post-configuration testing means you discover problems only when users report them. Avoid each of these mistakes deliberately and your VLAN deployment will function correctly from day one.
Conclusion
Setting up VLANs on a network switch transforms any home or business network from a flat, vulnerable single segment into a properly segmented, secure, and manageable infrastructure. The process requires a managed switch, a VLAN-capable router, a clear architecture plan, and the six configuration steps this guide covers. Follow each step carefully, test thoroughly, and document everything — your VLAN deployment will deliver the network security and control foundation your environment needs to remain protected as it grows.



Great breakdown of how VLANs enhance both security and network performanceVLAN Blog Comment Creation. One thing I’ve found helpful is using VLANs to isolate IoT devices, especially in environments with a mix of trusted and less-trusted hardware—it really tightens up control. Curious if you plan to dive deeper into VLAN trunking or inter-VLAN routing in a future post?