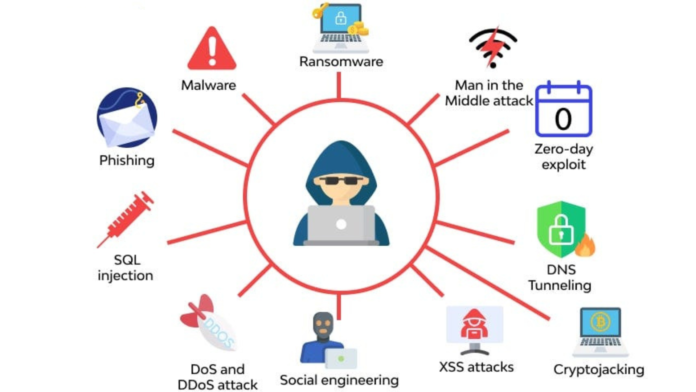
Cybersecurity threats are evolving faster than most organizations and individuals can track. Every day, attackers launch millions of attempts against personal devices, business networks, cloud infrastructure, and critical systems worldwide. Understanding the main types of security attacks in cybersecurity is not just academic knowledge — it is a practical foundation for making better security decisions, deploying the right defenses, and recognizing when your systems are under attack.
Phishing Attacks
Phishing remains the single most common entry point for cybersecurity attacks worldwide. Attackers send deceptive emails, text messages, or social media communications that impersonate trusted entities — banks, technology companies, government agencies, or colleagues — to trick recipients into revealing credentials, clicking malicious links, or downloading infected attachments.
Modern phishing attacks have grown far more sophisticated than the poorly written scam emails of a decade ago. Spear phishing targets specific individuals using personalized information gathered from social media and public sources. Whaling attacks target executives and high-value individuals with carefully researched communications designed to appear completely legitimate. Vishing uses phone calls rather than written messages, and smishing uses SMS text messages to deliver the same deceptive content.
Malware Attacks

Malware — malicious software — encompasses a broad category of attack tools that attackers install on target systems to achieve their objectives. Understanding the major malware subcategories clarifies the distinct threats each one poses.
Viruses attach themselves to legitimate files and spread when users share or execute those files across systems.
Ransomware encrypts a victim’s files or entire system and demands payment in cryptocurrency before providing the decryption key. Ransomware attacks against businesses, hospitals, schools, and government agencies have caused billions of dollars in damages annually and represent one of the most financially devastating cybersecurity threats organizations face today.
Trojans disguise themselves as legitimate software — a free application, a game, a utility tool — while secretly installing backdoors or additional malware components on the victim’s system.
Spyware silently monitors user activity, captures keystrokes, records credentials, and transmits sensitive information to attacker-controlled servers without the victim’s knowledge.
Rootkits embed themselves deep within an operating system — sometimes at the firmware or bootloader level — to hide their presence from antivirus tools and maintain persistent access to the compromised system.
Man-in-the-Middle Attacks
A man-in-the-middle attack occurs when an attacker secretly positions themselves between two communicating parties — intercepting, reading, and potentially modifying the data exchanged between them without either party realizing the communication is compromised.
Attackers execute man-in-the-middle attacks through several methods. ARP spoofing manipulates the Address Resolution Protocol on local networks to redirect traffic through the attacker’s device. Evil twin attacks create rogue Wi-Fi access points that mimic legitimate networks — when a user connects to the fake network, the attacker captures all their traffic. SSL stripping downgrades encrypted HTTPS connections to unencrypted HTTP, exposing login credentials and session data.
Denial of Service and Distributed Denial of Service Attacks
Denial of service attacks overwhelm a target system, server, or network with more traffic or requests than it can process, causing it to become unavailable to legitimate users. A distributed denial of service attack — DDoS — amplifies this by coordinating the attack traffic from thousands or millions of compromised devices simultaneously, making it far harder to mitigate by blocking a single source.
Attackers build botnets — large networks of compromised devices including computers, servers, and IoT devices — and direct them to flood targets with volumetric traffic, exploit protocol weaknesses, or exhaust application-layer resources. DDoS attacks disrupt online businesses, gaming services, financial platforms, and critical infrastructure, causing direct revenue loss and reputational dama
SQL Injection Attacks
SQL injection attacks target web applications and databases by inserting malicious SQL code into input fields — login forms, search boxes, URL parameters — that the application passes directly to its database without proper validation or sanitization.
When a SQL injection attack succeeds, the attacker manipulates the database query to bypass authentication, extract sensitive data including usernames and passwords, modify or delete database records, and in some configurations execute commands on the underlying server operating system. SQL injection consistently ranks among the most exploited web application vulnerabilities and has enabled some of the largest data breaches in history.
Social Engineering Attacks
Social engineering attacks manipulate human behavior rather than exploiting technical vulnerabilities. Attackers use psychological techniques — deception, authority, urgency, reciprocity, and fear — to convince targets to voluntarily perform actions that compromise security.
Social engineering is effective because it bypasses technical security controls entirely by targeting the human element. Security awareness training, strict verification procedures for sensitive requests, and a security culture that encourages questioning unusual instructions represent the most effective defenses against social engineering across all its forms.
Zero-Day Exploits
A zero-day exploit targets a software vulnerability that the developer does not yet know about — or has not yet patched — giving defenders zero days to protect their systems before attacks begin. Attackers discover these vulnerabilities through their own research, purchase them from specialist brokers, or acquire them from other threat actors.
Zero-day exploits are among the most dangerous cybersecurity attack types because no patch exists at the time of exploitation. They frequently appear in targeted attacks against high-value organizations, government systems, and critical infrastructure. State-sponsored threat actors and sophisticated criminal organizations invest heavily in acquiring and weaponizing zero-day vulnerabilities.
Insider Threats
Insider threats originate from individuals who already have legitimate access to systems and data — employees, contractors, former staff, or business partners. Malicious insiders intentionally steal data, sabotage systems, or sell access to external attackers. Negligent insiders cause security incidents unintentionally through poor security practices, misconfiguration, or falling victim to phishing.
Insider threats are particularly difficult to detect because the attacker uses legitimate credentials and access pathways that security tools are configured to trust. Organizations defend against insider threats through the principle of least privilege — granting each user only the minimum access their role requires — combined with user behavior analytics, access logging, and regular access reviews that identify unusual patterns before they escalate into full security incidents.
Advanced Persistent Threats
Advanced persistent threats — APTs — represent the most sophisticated category of cybersecurity attack. Nation-state actors and highly organized criminal groups conduct APT campaigns that maintain long-term covert access to target networks — sometimes for months or years — while systematically exfiltrating valuable data, conducting espionage, or positioning for future destructive action.
APT attackers use a combination of spear phishing for initial access, custom malware for persistence, lateral movement techniques to expand access across the network, and sophisticated evasion methods to avoid detection by security tools. Their patience and resource level distinguishes them from opportunistic attackers — APT groups conduct extensive reconnaissance before attacking and adapt their techniques when defenders respond.
Conclusion
Understanding the main types of security attacks in cybersecurity gives you a practical foundation for building effective defenses rather than reacting to threats after they materialize. Phishing, malware, man-in-the-middle attacks, DDoS, SQL injection, social engineering, zero-day exploits, insider threats, and advanced persistent threats each operate through different mechanisms and require different defensive responses. No single security tool stops all of them.