Network segmentation divides a computer network into smaller, isolated subnetworks that control traffic flow and limit unauthorized access. US businesses adopt network segmentation to strengthen their cybersecurity posture, contain breaches, and meet strict regulatory requirements like PCI DSS and HIPAA. Companies that ignore this strategy expose themselves to lateral movement by ransomware and insider threats. They also suffer from network congestion and compliance violations.
Business leaders implement network segmentation because flat networks create a single massive broadcast domain that attackers exploit in seconds. Instead, they divide the network into segments, subnets, and subnetworks using firewalls, VLANs, and access control lists. This approach delivers immediate improvements in performance and security. Organizations achieve defense in depth while they simplify network management and protect sensitive data.
Table of Contents
What Is Network Segmentation?
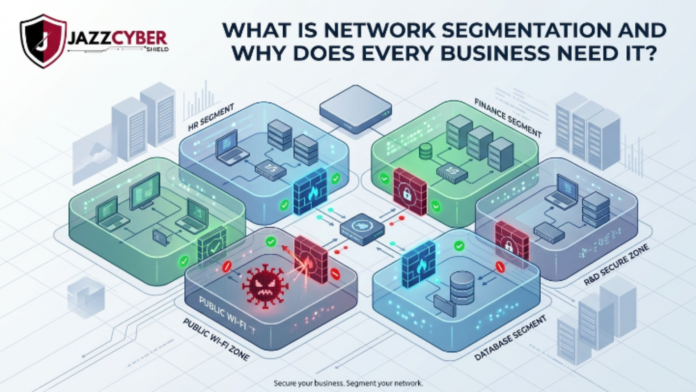
Network segmentation creates isolated zones within your infrastructure so devices and applications communicate only when explicitly permitted. IT teams use physical segmentation with separate hardware, logical segmentation through VLANs, or software-defined networking segmentation via policies. They achieve network partitioning, network isolation, or network segregation depending on the chosen method.
In practice, administrators divide the network into segments based on departments, applications, or data sensitivity. They enforce rules with firewalls and access control lists. This process prevents east-west traffic from spreading malware across the entire environment. US companies shift from flat networks to segmented architectures because they recognize that a single breach in an unsegmented network can compromise every connected device.
Network Segmentation Explained: Macro vs. Micro
Macro segmentation groups resources by broad categories such as departments or locations. Microsegmentation applies granular policies down to individual workloads or applications. Both strategies improve upon traditional flat networks, yet they differ in scope and enforcement.
Application segmentation isolates specific software environments, while zero trust segmentation verifies every request regardless of origin. VLAN segmentation remains popular for logical isolation, and physical segmentation uses dedicated switches and routers for air-gapped environments.
Network segmentation explained also covers network partitioning techniques that reduce broadcast domains and limit congestion. Teams monitor traffic flow control in real time and adjust segments dynamically with software-defined tools. This flexibility supports hybrid cloud security and modern workloads.
Why Network Segmentation Is Important for US Businesses
US businesses face escalating cyber threats that demand proactive defense. Network segmentation delivers critical protection by containing breaches and preventing ransomware from encrypting the entire network. Regulators enforce strict standards, and non-compliance triggers massive fines.
Network segmentation security directly addresses PCI DSS requirements for isolating cardholder data environments. It also supports HIPAA by protecting electronic protected health information through workload isolation. Organizations achieve regulatory compliance while they reduce the scope of annual audits.
Moreover, network segmentation for business improves operational efficiency. IT teams gain visibility into traffic patterns, enforce least-privilege access, and respond faster to incidents. They limit the blast radius of attacks and protect sensitive data from both external hackers and insider threats.
Key Benefits of Network Segmentation
Businesses that deploy network segmentation enjoy these measurable advantages:
- Reduce attack surface by isolating critical assets and blocking unauthorized lateral movement.
- Prevent lateral movement during breaches so attackers cannot pivot from one segment to another.
- Breach containment keeps incidents localized and enables rapid recovery.
- Limit blast radius of ransomware and malware through immediate isolation.
- Improve network security and overall cybersecurity posture with layered controls.
- Enhance access control using firewall rules and dynamic policies.
- Reduce network congestion by shrinking broadcast domains and optimizing traffic flow.
- Improve performance for applications and end users through dedicated bandwidth per segment.
- Achieve regulatory compliance with PCI DSS, HIPAA, and other US standards.
- Protect sensitive data by enforcing strict boundaries around financial, customer, and intellectual property systems.
- Support defense in depth by adding multiple layers of security controls.
- Enable ransomware protection and malware containment at the network level.
- Mitigate insider threat prevention through granular monitoring and access restrictions.
- Simplify network management with centralized policy enforcement and automated tools.
Network segmentation advantages extend to cost savings on bandwidth, faster troubleshooting, and easier scalability. Companies report up to 50% reduction in incident response time after proper implementation.
Network Segmentation vs. Microsegmentation: Technical Comparison
| Feature | Traditional Network Segmentation (Macro) | Microsegmentation | Flat Network (No Segmentation) |
|---|---|---|---|
| Granularity | Department or zone level | Workload or application level | None |
| Enforcement | Firewalls and VLANs | Software-defined policies | None |
| Attack Surface Reduction | Moderate | Maximum | None |
| Lateral Movement Prevention | Good | Excellent | None |
| Performance Impact | Low | Minimal with modern tools | High congestion |
| Compliance Support | Strong for PCI DSS/HIPAA | Ideal for zero trust | Fails audits |
| Implementation Complexity | Medium | Higher but automated | None |
| Best For | Mid-size networks | Cloud, containers, hybrid environments | Small, low-risk setups |
This table highlights why forward-thinking US organizations move beyond basic network segmentation to zero trust segmentation and microsegmentation for maximum protection.
How to Implement Network Segmentation: Step-by-Step Guide
IT professionals follow this network segmentation guide and network segmentation tutorial to deploy effectively:
- Inventory assets and map data flows to identify sensitive systems.
- Define segmentation goals based on risk, compliance, and performance needs.
- Choose segmentation method — physical, logical (VLAN), or software-defined.
- Design subnets and segments using tools like IP subnet calculators.
- Configure firewall rules and access control lists to enforce traffic policies.
- Implement monitoring for east-west traffic and anomaly detection.
- Test thoroughly in a staging environment before production rollout.
- Document and automate policies for ongoing management.
For practical network segmentation best practices with next-generation firewalls, explore our Next-Generation Firewall (NGFW): The Complete Guide for 2026. Teams also leverage free tools during planning — discover the Best Free Network Security Tools for IT Professionals in the USA (2026 Guide) that include an enterprise-grade IP Subnet Calculator.
Network Segmentation Cybersecurity Best Practices
Experts recommend these proven tactics to maximize network segmentation cybersecurity:
- Apply the principle of least privilege across every segment.
- Monitor all east-west traffic continuously with advanced analytics.
- Update firewall rules regularly to reflect changing business needs.
- Combine network segmentation with zero trust architecture for stronger controls.
- Segment IoT and OT networks separately to prevent device-based attacks.
- Use software-defined networking segmentation for dynamic cloud environments.
- Conduct regular penetration tests to validate segmentation effectiveness.
Network isolation and network segregation become force multipliers when paired with strong identity controls and continuous monitoring.
Network Segmentation for Cloud, IoT, and OT Environments
Hybrid cloud security demands cloud network segmentation that spans AWS, Azure, and on-premises infrastructure. Workload isolation protects containers and serverless functions from lateral threats.
IoT segmentation isolates smart devices on dedicated VLANs to stop compromised cameras or sensors from reaching corporate systems. OT network segmentation safeguards industrial control systems in manufacturing and energy sectors where downtime is unacceptable.
Businesses achieve these outcomes by deploying consistent policies across all environments and using centralized management consoles.
FAQ
What is network segmentation and how does it differ from a flat network? Network segmentation divides your infrastructure into isolated subnetworks while a flat network allows unrestricted communication across all devices. Segmented architectures reduce risk and improve performance dramatically.
Why is network segmentation important for cybersecurity? It prevents lateral movement, contains breaches, and limits the blast radius of attacks. Organizations reduce their attack surface and strengthen defense in depth.
What are the main benefits of network segmentation for business? Businesses gain improved security, regulatory compliance, better performance, simplified management, and significant cost savings on audits and incident response.
How do I implement network segmentation in my organization? Start with asset inventory, define clear policies, configure firewalls and VLANs, test thoroughly, and monitor continuously. Follow our step-by-step guide above.
What is the difference between network segmentation and microsegmentation? Network segmentation operates at the macro level with broader zones, while microsegmentation enforces policies at the individual workload level for maximum granularity and zero trust security.
Conclusion
Network segmentation stands as a non-negotiable foundation for modern US business cybersecurity. Organizations that implement network segmentation today protect themselves against tomorrow’s threats while they achieve compliance, boost performance, and simplify operations. They move from vulnerable flat networks to secure, manageable architectures that scale with growth.
Every IT leader and business owner must evaluate their current infrastructure and begin segmentation planning immediately. The tools, best practices, and technologies exist right now to deliver network segmentation advantages that directly impact the bottom line.
Ready to strengthen your defenses? Explore enterprise-grade Fortinet, SonicWall, and WatchGuard firewalls designed for seamless network segmentation at Jazz Cyber Shield Firewalls. Pair them with our expert guidance and free network tools to build a resilient, future-proof security posture.
Protect what matters most. Segment your network today and secure your business for tomorrow.