These days, considering how rapid digital technologies are advancing, one can never neglect cybersecurity. MitM attacks or spoofing is among the most prevalent and severe forms of attacks today. Spoofing is the act of pretending as another human being or a device to be able to trespass into someone’s system or network. We will talk about what spoofing attacks are, how they operate, and how you can enhance the safety of your system against such problematic accesses.
What is a Spoofing Attack?
Spoofing attacks use impersonation in an attempt to deceive authentic entities thereby compromising the network security. Even if there are several layers of security, impersonation manages to get through. The common types of attacks include:
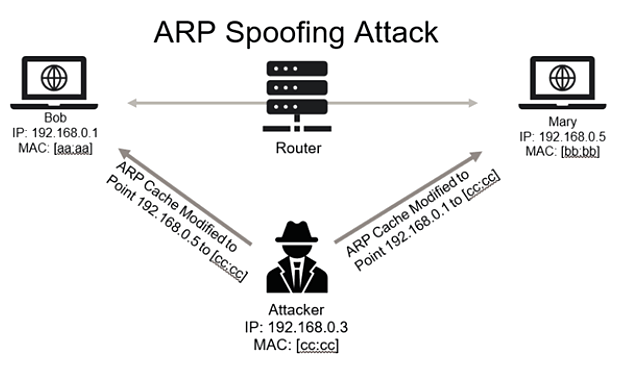
- IP Spoofing: The attack involves changing the source IP address in a given packet to give the impression that it originates from a trusted source.
- MAC Spoofing: The MAC address of one’s hardware gets changed to imitate another misplaced MAC address from within the network.
- DNS Spoofing: Impulse manipulation of DNS records to deflect traffic to an evil endpoint.
What Role Does Network Switch Play in Trooping Attack?
Essentially, too often are spoofing attacks directed at network switches through the channel of flood-packeting that subverts its right decision-making path of forwarding data; several unspeakable risks arise from there: network downtime, information leakage, unauthorized access, and so on.
Cybercriminals actively use spoofing tactics to sidestep such security measures. Know how you can engender protection for your systems.

One of the more traditional attacks against the network switches is the MAC address loading attacks. In this attack, the attacker submits thousands or an endless number of totally fake MAC addresses to the switch, thereby filling the MAC address table. Then, once this table gets full, the switch starts broadcasting traffic to all devices on a network instead of forwarding it correctly. Attackers use this weak point to hijack the sensitive data or involve in other malicious actions.
Risks of Spoofing Attacks
Spoofing attacks can prove to be dangerous to human individuals in many aspects and organizations from a business viewpoint. Some of the risks that are commonly associated with spoofing include:
- Data Interception: Attackers are able to intercept and view sensitive information straying from login credentials to personal details and financial information.
- Network Downtime: Spoofing attacks will bash a network with a lot of traffic, rendering the systems unresponsive and slowing down everyday operations.
- Unauthorized Access: Such attacks allow unauthorized access to attacker systems and ending up in data theft, loss, or manipulation.
- Reputation Damage: In purely business terms, spoofing dents a reputation and loses customer trust.
Stopping Attacks by Spoofing
The task of preventing spoofing attacks can take on multiple pathways, whereas, certainly, leading tried-and-true stock head-paved ways to secure your network involves:
- Secure Network Switches: Modern switches are equipped with built-in tamper-resistant features that assist secure it with port security and DHCP snooping aiding in securing the endpoint as well as the network from against device-entry from unauthorized sources and also drop the possibility of MAC flooding attacks.
- Consider VLANs: If you separate your whole infrastructure by VLANs, you protect particular systems and put up barriers so that attackers cannot have access to the entire network.
- IDS/IPS Systems: These detect threats and automate alerts or restrictions to prevent network attacks.
- Encrypted Data: Encrypting data in transit prevents attackers from accessing sensitive information.
- Regular Updates: Updating firmware and security patches closes vulnerabilities before exploitation.
- Educate Your Team: Whatever you do in the technical field, understand that security training for employees and end-users is of immense importance. Teach them about what phishing is, and the negative sides of email spoofing. Provide training that instructs them on the importance of being watchful while opening an email or clicking a weblink from an unknown source.

Why Opt for Jazz Cyber Shield for Network Security?
Combining with Seagate as an authorized dealer, it is yet another satisfaction for Jazz Cyber Shield. Network switches or the feature-loaded storage solutions will both come in handy.
It is our way of dedication and assurance by ensuring top cybersecurity degrees and making sure that they bring in effect measures that are tailor-made to meet the client’s specifications. Refer to Jazz Cyber Shield so that you get expert help in securing your infrastructure against spoofing attacks and other network vulnerabilities.




Spoofing is such a persistent threat these days. I think it’s interesting how much social engineering can play a role in these attacks too. Awareness training for employees is just as important as technical defenses.
Great breakdown on spoofing—many people underestimate how easily attackers can disguise themselves to slip into a network. One point worth emphasizing is that spoofing often works best when paired with social engineering, so training staff to recognize suspicious requests can be just as critical as the technical defenses. Combining awareness with layered security really makes the difference.
Nice post on spoofing. It’s always eye-opening to consider how impersonation can trick both users and systems. I think another important step is ensuring that all communication channels are encrypted—it’s a simple yet effective line of defense.
Great breakdown of spoofing attacks—it’s alarming how easily attackers can impersonate trusted sources to infiltrate networks. One thing that might be worth adding is how social engineering often plays a role alongside technical spoofing, making user education just as critical as system-level defenses.
Great breakdown of spoofing and its impact on network security! One point that really stood out is the importance of implementing multi-factor authentication to add an extra layer of protection. I’ve found it can make a big difference in preventing unauthorized access.
I found this blog on preventing spoofing attacks to be extremely informative. The step-by-step guide on how to protect my network from these types of attacks was exactly what I needed. The explanations were clear, and the security recommendations were practical and easy to implement. Jazz Cyber Shield really knows how to break down complex security topics. I feel much more confident in securing my network now!
Spoofing attacks are becoming increasingly common, and it’s good to see more awareness being raised. Implementing encryption and multi-factor authentication could make a big difference in preventing these attacks from succeeding.
Good reminder about the risks of spoofing attacks. It’d be helpful to also touch on how employee training plays a role in prevention—human error often opens the door.
Really appreciate the focus on how spoofing attacks often exploit trust—especially in the context of Man-in-the-Middle tactics. It might also be helpful to touch on how user education and internal phishing simulations can strengthen a network’s human firewall. Looking forward to future posts diving deeper into layered security strategies.
This post does Blog Comment Creation Guide a solid job highlighting the seriousness of spoofing attacks, especially how they often go hand-in-hand with man-in-the-middle strategies. One aspect worth expanding on is the human factor—educating users to spot phishing emails or suspicious login prompts can significantly reduce entry points for spoofers.
Really Blog Comment Creation appreciate the breakdown on spoofing attacks—so many people still think of them as just email scams, but the post does a great job highlighting how they can involve device impersonation too. One thing that might be helpful to explore further is how DNS spoofing differs from ARP spoofing in terms of impact and detection. Thanks for shedding light on such a relevant threat!
Spoofing can be so difficult to detect since attackers can easily masquerade as trusted users or devices. Implementing network monitoring and verifying device identities seem crucial to reduce the risks.
Excellent guide! I found the tips on verifying source addresses and using proper authentication protocols really useful for keeping networks safe.