The Palo Alto PAN-OS zero-day tracked as CVE-2026-0300 has pushed network defenders into one of the worst possible scenarios of 2026: a critical, unauthenticated remote code execution flaw in a perimeter firewall, with confirmed active exploitation, no patch available, and a federal mitigation deadline already in effect. Shadowserver Foundation has identified more than 5,800 PAN-OS VM-Series firewalls exposed to the public internet, and CISA has placed the bug in its Known Exploited Vulnerabilities catalog with a May 9, 2026 deadline for federal agencies. eSentire
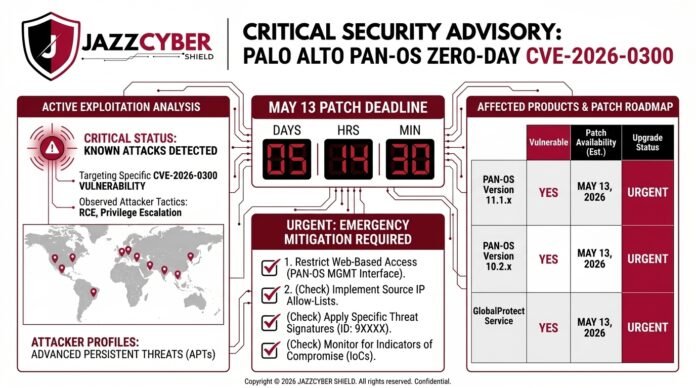
If you operate a PA-Series or VM-Series firewall, this is not a “wait for the next maintenance window” situation. The first official fixes are not expected until May 13, 2026, which leaves a hard five-day window where configuration hardening is the only line of defense. This guide breaks down what the Palo Alto PAN-OS zero-day actually does, who is exploiting it, and the exact mitigation steps your team should run today.
The User-ID Authentication Portal was never meant to live on the public internet — and the attackers behind CVE-2026-0300 are proving it.
Table of Contents
What Is the Palo Alto PAN-OS Zero-Day CVE-2026-0300?
The Palo Alto PAN-OS zero-day is a buffer overflow in the User-ID Authentication Portal, the component most engineers know as the Captive Portal. Palo Alto rates the flaw 9.3 out of 10 when the portal is exposed to the internet or other untrusted networks, dropping to 8.7 if access is restricted to trusted internal IPs. The vulnerability is classified as CWE-787, an out-of-bounds write — the same memory corruption family responsible for many of the most damaging firewall bugs of the past decade. SOC Prime
Three details make this particular Palo Alto PAN-OS zero-day uniquely dangerous:
- No authentication required. An unauthenticated attacker can execute arbitrary code with root privileges by sending specially crafted packets. Help Net Security
- Exploitation is automatable. Palo Alto has confirmed the bug can be triggered programmatically, which removes any practical safety from low attack volume.
- Edge devices, not cloud. Prisma Access, Cloud NGFW, and Panorama appliances are not affected — the impact is limited to the on-premise PA-Series hardware and VM-Series virtual firewalls many small and mid-market businesses run as their primary perimeter. Unit 42
Root-level RCE on a perimeter firewall is the worst case for any defender. Once attackers control the firewall, they own routing, identity mappings, VPN sessions, and in many cases the trust boundary that internal services rely on.
How Attackers Are Exploiting the Palo Alto PAN-OS Zero-Day Right Now
This is not a theoretical bug. Palo Alto’s Unit 42 team is tracking a cluster called CL-STA-1132, which appears to be state-sponsored. The attack timeline they published reads like a textbook APT operation rather than opportunistic scanning.
Initial unsuccessful attempts began on April 9, 2026, followed a week later by successful remote code execution and shellcode injection into the nginx worker process. From there, the operators moved methodically: Unit 42
- Anti-forensic cleanup first. Crash kernel messages, nginx crash entries, and core dump files were wiped within minutes of compromise.
- Tooling deployment with root. Four days post-compromise, the attackers deployed publicly available tunneling utilities — EarthWorm and ReverseSocks5 — to maintain covert access.
- Active Directory enumeration. Using the firewall’s service account, the operators enumerated domain root and DomainDnsZones objects, which is the reconnaissance phase of nearly every modern ransomware playbook.
- Evidence destruction. ptrace injection traces and SetUserID privilege escalation binaries were deleted before disengagement.
This is not a smash-and-grab. The CL-STA-1132 cluster’s behavior matches the playbook we documented in our SonicWall and Fortinet firewall attacks 2026 breakdown, where edge device compromise feeds directly into Active Directory takeover. The Palo Alto PAN-OS zero-day appears to be the next entry point in the same campaign-style targeting of SMB and government networks.
Which Firewalls Does the Palo Alto PAN-OS Zero-Day Affect?
The vulnerability only matters if two conditions are true on your device. The platform is PA-Series or VM-Series, and the User-ID Authentication Portal (Captive Portal) is enabled.
The affected PAN-OS branches are 10.2, 11.1, 11.2, and 12.1. The first round of fixed builds is expected around May 13, 2026, with a second round of releases scheduled around May 28. Until those builds drop, every internet-facing device with the portal enabled is in the exposure window. Help Net Security
A few critical exclusions worth confirming with your team:
- Cloud NGFW — not affected.
- Prisma Access — not affected.
- Panorama management appliances — not affected.
If you cannot easily tell whether the portal is enabled, that is itself the answer to your first action item — log into the device and verify under Device > User Identification > Authentication Portal Settings.
Emergency Mitigation Steps Before the May 13 Patch
Patches are the destination, but configuration hardening is what gets you there alive. The following five steps are taken directly from Palo Alto’s advisory and Unit 42’s threat brief, sequenced for IT teams that need to act fast.
Step 1: Verify Whether the Captive Portal Is Enabled
Open the PAN-OS web UI. Navigate to Device > User Identification > Authentication Portal Settings. If the portal is disabled and you do not need it, leave it disabled. If it is enabled, continue to step two.
Step 2: Restrict Access to Trusted Internal Zones Only
This is the single highest-impact mitigation. Lock the portal down so it is reachable only from internal, trusted network segments. Palo Alto explicitly states that customers following standard hardening practices are at greatly reduced risk. IT-Connect –
If your portal currently accepts traffic from any L3 interface that touches the internet, that needs to change today.
Step 3: Disable Response Pages on Internet-Facing L3 Interfaces
In the Interface Management Profile attached to every L3 interface where untrusted or internet traffic ingresses, disable Response Pages. Keep Response Pages enabled only on interfaces sitting in trusted internal zones where legitimate browsers should land.
Step 4: Disable the Captive Portal Entirely if You Do Not Need It
Many networks enabled the User-ID Authentication Portal years ago and never decommissioned it. If you can validate that no production workflow currently depends on captive portal authentication, the cleanest mitigation is to disable it outright. The setting lives in the same Authentication Portal Settings screen.
Step 5: Enable the Threat Prevention Signature
Customers with an Advanced Threat Prevention subscription should enable Threat ID 510019 from Applications and Threats content version 9097-10022 or later. Decoder capabilities require PAN-OS 11.1 or later for this Threat ID to function. This will not replace patching, but it does block known exploitation traffic patterns while you wait for fixed builds. Unit 42
Patch Timeline for CVE-2026-0300
The fix release schedule is staggered across two waves. Here is the rolled-up view your patching team needs:
| Wave | Approx. Release Date | Affected Branches |
|---|---|---|
| Wave 1 | May 13, 2026 | 10.2.10-h36, 11.1.4-h33, 11.1.6-h32, 11.1.10-h25, 11.1.13-h5, 11.2.7-h13, 11.2.10-h6, 12.1.4-h5 |
| Wave 2 | May 28, 2026 | 10.2.7-h34, 10.2.13-h21, 10.2.16-h7, 11.1.7-h6, 11.1.15, 11.2.4-h17, 11.2.12, 12.1.7 |
If your firewall does not appear in Wave 1, do not assume you can wait passively until Wave 2. The mitigation steps above remain mandatory until your specific build receives a fix.
Why This Palo Alto PAN-OS Zero-Day Matters for SMBs
Three high-severity firewall bugs have hit production networks in 2026 alone: the SonicWall SonicOS authentication bypass we covered in our SonicWall CVE-2026-0204 patch breakdown, the SonicWall and Fortinet attack wave that hit 56% of compromised networks, and now this Palo Alto PAN-OS zero-day.
The pattern is unmistakable. Edge security appliances are the highest-value target on most networks, because compromise yields:
- Root-level access to a device that sees every authentication, every routing decision, and every VPN session.
- A pivot point into Active Directory through service account credentials the firewall already holds.
- A position from which to disable logging, mute alerts, and remain undetected for weeks.
For SMBs without a dedicated SOC, this matters even more. A single zero-day in your perimeter firewall can collapse your entire defense plan if you do not have layered controls. Our zero trust network security guide for 2026 walks through the architectural mindset that limits blast radius when one device falls — and it is the strategy IT teams running Palo Alto, Fortinet, or SonicWall hardware should be moving toward.
How to Harden Your Firewall Stack Today
A zero-day cannot be predicted. What you can control is whether your network is built to survive one.
Three practical investments will pay off the next time a Palo Alto, Fortinet, SonicWall, or WatchGuard advisory drops at 6 PM on a Friday:
- Reduce internet-exposed services. If the portal does not need to be public, it should not be public. The same logic applies to management interfaces, SSL VPN portals, and admin consoles across every brand.
- Add a second layer. Single-vendor dependency is the most common gap in SMB networks. Pairing a primary perimeter firewall with a segmentation layer or upgraded next-gen appliance limits how far one compromised device can take an attacker. Our best firewall for small business 2026 buyer’s guide compares the leading enterprise options on AI-aware threat prevention, SSL inspection depth, and Zero Trust readiness.
- Stay current on inventory. Many organizations exposed to the Palo Alto PAN-OS zero-day today will discover they had Captive Portal enabled on a forgotten branch device. Quarterly configuration audits beat post-incident scrambles every time.
If you are evaluating a firewall refresh, we are an authorized reseller for Fortinet next-gen firewalls, SonicWall NGFW appliances, and WatchGuard firewall solutions — and we can scope a deployment that does not leave critical services exposed by default. The full catalog of enterprise-grade firewall solutions is sortable by performance tier, throughput, and licensing model.
Frequently Asked Questions
Is the Palo Alto PAN-OS zero-day patched yet?
No. As of May 9, 2026, no official patch is available. The first fixed builds are scheduled to begin rolling out on May 13, 2026, with a second wave around May 28, 2026. Configuration mitigation is the only effective defense in the interim. IT-Connect –
What is the CVSS score for CVE-2026-0300?
The score is 9.3 when the User-ID Authentication Portal is exposed to the internet or untrusted networks, and 8.7 when access is restricted to trusted internal IPs only. Both scores fall in the Critical/High range.
Does the Palo Alto PAN-OS zero-day affect Cloud NGFW or Panorama?
No. The vulnerability impacts only PA-Series hardware and VM-Series virtual firewalls running PAN-OS with the Captive Portal enabled. Prisma Access, Cloud NGFW, and Panorama management appliances are unaffected.
Are SonicWall, Fortinet, or WatchGuard firewalls affected by this Palo Alto PAN-OS zero-day?
No. CVE-2026-0300 is specific to Palo Alto Networks PAN-OS software. However, all major firewall brands have faced their own critical vulnerabilities in 2026, which is why a layered, brand-agnostic security strategy is the safer approach for SMB and enterprise networks.
How can I check whether my Palo Alto firewall is exposed to CVE-2026-0300?
Log into the PAN-OS administrative interface and navigate to Device > User Identification > Authentication Portal Settings. Confirm whether the portal is enabled and review the interfaces it is reachable from. If any internet-facing L3 interface can ingress to the portal, your device is in the exposure window until the patch is applied.
Has CISA added the Palo Alto PAN-OS zero-day to the KEV catalog?
Yes. CISA added CVE-2026-0300 to the Known Exploited Vulnerabilities catalog on May 6, 2026, with a federal mitigation deadline of May 9, 2026. Federal Civilian Executive Branch agencies are required to apply the fixes or mitigations by that date. The Hacker News
The Bottom Line on the Palo Alto PAN-OS Zero-Day
Five days is not a long time to wait for a patch when state-sponsored operators are already inside other people’s networks using the same bug. The Palo Alto PAN-OS zero-day is a textbook reminder that every internet-exposed authentication surface is a potential RCE vector, and that the discipline of restricting administrative and identity portals to trusted zones is not optional.
Run the five mitigation steps today. Subscribe your team to Palo Alto’s advisory updates so you catch Wave 1 patches the moment they ship on May 13. And if this incident has surfaced gaps in your perimeter strategy, it is the right time to evaluate whether your firewall stack is positioned to survive the next zero-day — not just this one.
Sources & Authoritative References:
- Palo Alto Networks Official Security Advisory for CVE-2026-0300
- CISA Known Exploited Vulnerabilities Catalog
- Unit 42 Threat Brief: PAN-OS Captive Portal Zero-Day