From AI-powered ransomware and nation-state router exploits to NDAA camera bans and VLAN segmentation — everything you need to protect your network right now.
Cybersecurity 2026 is no longer a single-domain problem. It is a converged challenge that spans your network switches, your IP cameras, your cloud stack, and every IoT endpoint in between. This cybersecurity 2026 guide gives you the exact threat landscape, defensive playbook, and hardware compliance requirements your organisation needs this year.
If your organisation owns a network switch and a security camera — and virtually every business does — you are already sitting at the intersection of three of the most actively targeted threat surfaces in 2026. Cybersecurity professionals are tracking over 2.4 million X/Twitter posts a day about data breaches, ransomware, and AI-driven attacks. Network switch vulnerabilities spiked after Cisco’s critical April advisory. And the debate over NDAA-compliant security cameras has moved from a niche government concern to a mainstream business risk.
This guide connects all three topics into one actionable framework. We cover the current threat landscape, show you exactly how to harden your switches and cameras, and point you to resources on JazzCyberShield.com. Whether you run a small business or manage enterprise infrastructure, this article has something for you.
Section 1
The Biggest Cybersecurity Threats of 2026
The World Economic Forum’s Global Cybersecurity Outlook 2026, drawing on 800 global leaders, found AI-related vulnerabilities are the fastest-growing risk of the year. The report warns of a widening “cyber equity” gap — well-resourced organisations pull ahead while smaller players are left exposed. Understanding where attacks originate is the first step toward stopping them.
1. AI-Powered Ransomware
Ransomware has evolved far beyond file encryption. Modern campaigns combine data theft, DDoS pressure, and compliance violation threats — a model called triple extortion. AI has cut median dwell time inside a compromised network from nine days to just five. Ransomware-as-a-Service (RaaS) platforms allow any threat actor to deploy attacks with enterprise-grade efficiency. The construction sector saw a 44% year-over-year increase in victims in Q1 2026 alone.
For a full breakdown, read our complete guide to cybersecurity threats in 2026.
Prior compromise is now the #1 initial ransomware infection vector (30% of cases), doubling from 2024 levels. If attackers already have a foothold in your network, they will find the crown jewels.
2. Supply Chain Attacks
IBM’s X-Force Threat Intelligence Index 2026 reveals major supply chain and third-party breaches have quadrupled over five years. The Vercel breach in April 2026 — where a compromised third-party AI tool accessed internal systems — is a textbook example. Your security posture is only as strong as your least-secure supplier.
3. Zero-Day Exploitation at Record Speed
Mandiant’s M-Trends 2026 documents a mean time to exploit of –7 days — exploitation regularly occurs before a vendor even knows the vulnerability exists. NIST limited CVE enrichment in April 2026 after a 263% surge in submissions. Traditional quarterly patch cycles are no longer viable.
4. Nation-State Attacks on Network Infrastructure
Russian GRU units were confirmed in April 2026 to be exploiting flaws in older internet routers to silently harvest Microsoft Office authentication tokens from over 18,000 networks — without deploying any malware. Nation-state actors are increasingly targeting legacy network devices, making network switch security a direct national-security concern.
“In 2026, attackers are shifting their attention to the systems that bridge the physical and digital world: cameras, sensors, AI models, and the systems that connect them.”
— Network Optix Cybersecurity Report 20265. IoT and Physical Device Vulnerabilities
Ninety percent of enterprises encountered risky AI interactions within a three-month period in 2026 (Check Point). Unmanaged IoT devices — including security cameras and network switches — are routinely used as persistent launch bases for lateral movement across entire networks. Learn how AI-powered firewalls are countering these threats in our AI Firewall Security guide.
Section 2
How to Secure Your Network Switches in 2026
Network switches are the backbone of every enterprise and SMB network. Gaining access to one gives an attacker a pathway to an entire network segment. The Cisco critical vulnerability CVE-2026-20184 (CVSS 9.8) — which allowed unauthenticated remote attackers to impersonate any Webex user — was a stark reminder of how dangerous unpatched switch infrastructure can be.
Why Switches Are a Primary Attack Target
Switches may not host data directly, but they transport it. Once penetrated, a switch can be programmed to mirror and offload critical traffic for attackers to parse for credentials and session tokens. In many networks, surveillance systems share the same switch as corporate servers — meaning a compromised camera becomes a direct route into your core infrastructure.
Using default VLAN 1 for production traffic is one of the most widespread dangerous misconfigurations. Every attacker knows VLAN 1 is the factory default. Never use it for live traffic.
VLAN Segmentation: Your Most Powerful Switch Security Tool
VLANs (Virtual Local Area Networks) create isolated logical groups of devices. When properly configured, VLAN segmentation severely limits lateral movement — the primary technique attackers use to escalate a small compromise into a full breach. IBM data shows lateral movement contributes to nearly 25% of all breaches.
vlan 10 name Corporate
vlan 20 name Cameras_IoT
vlan 30 name Servers
vlan 40 name Guest_WiFi
vlan 99 name Management
! Isolate camera/IoT port
interface GigabitEthernet0/5
switchport mode access
switchport access vlan 20
spanning-tree portfast
! Move management off VLAN 1
interface vlan 99
ip address 192.168.99.1 255.255.255.0
no shutdown
8 Steps to Harden Your Network Switches
- Never use VLAN 1 for production traffic. Create dedicated VLANs — every attacker knows VLAN 1 is the default.
- Move the management VLAN to a dedicated isolated VLAN (e.g., VLAN 99) so compromised workstations cannot reach switch admin interfaces.
- Disable all unused switch ports and assign them to a quarantine VLAN — unused ports are open doors.
- Enable 802.1X port authentication so only authorised devices can connect.
- Apply firmware updates immediately — Cisco CVE-2026-20184 scored CVSS 9.8. Hours matter.
- MFA on all admin accounts. Update credentials whenever access-enabled staff leave.
- Physically lock all switches in secured rooms. Physical access equals full network access.
- Segment camera and IoT traffic from corporate systems using separate VLANs and strict ACLs.
VLAN vs. Microsegmentation: When to Upgrade
Traditional VLANs are a strong foundation, but accumulate allow-rules over time — creating the “Swiss cheese effect.” For organisations with significant IoT or cloud footprints, software-defined microsegmentation enforces policies based on application identity and user context, not just IP addresses. Browse our network security resources for full strategy guides.
Section 3
Security Cameras: IoT Risks, NDAA Compliance & the 2026 Landscape
There is an uncomfortable irony at the heart of physical security: the cameras installed to protect your premises are frequently among the most vulnerable devices on your network. In March 2026, CISA added CVE-2017-7921 — a critical authentication bypass in Hikvision cameras discovered in 2017 — to its Known Exploited Vulnerabilities catalog after confirming active exploitation in the wild. Nine years after discovery, enough unpatched devices remained deployed that a federal advisory was necessary.
CVE-2017-7921 in Hikvision cameras is actively being exploited. If your cameras cannot receive firmware updates, they must be replaced — not left on your network.
The NDAA Ban: What It Means for Your Business
NDAA Section 889 explicitly prohibits federal agencies, contractors, and grant recipients from using video surveillance equipment from Hikvision, Dahua, Huawei, ZTE, and Hytera — including white-label products built on banned chipsets like HiSilicon SoC.
| Brand | Country | NDAA Status | Notes |
|---|---|---|---|
| Hikvision | China | ❌ Non-Compliant | Banned — federal agencies & contractors |
| Dahua / Lorex | China | ❌ Non-Compliant | Banned — Lorex is Dahua-owned |
| Axis Communications | Sweden | ✓ Compliant | Enterprise & government recommended |
| Hanwha Vision | South Korea | ✓ Compliant | Commercial & government approved |
| Avigilon / Motorola | US / Canada | ✓ Compliant | Enterprise & law enforcement grade |
| Bosch Security | Germany | ✓ Compliant | Industrial & enterprise approved |
| Reolink | China | ⚠ Verify | Consumer / SMB — verify chipset first |
The FCC conducted a significant enforcement push in late 2025 and early 2026, leading to widespread retail delistings. Beyond federal contractors, cyber insurance providers are now explicitly asking about camera brand compliance — non-NDAA-compliant hardware may result in higher premiums or claim denials.
2026 Camera Security Trends
- On-device AI processing: Person detection, licence plate recognition, and anomaly detection run directly on the device, eliminating cloud transmission and reducing interception risk.
- Subscription-free local storage: MicroSD and NVR storage remove cloud dependency, keeping footage under direct organisational control.
- Secure boot and encrypted streams: NDAA-compliant manufacturers now ship hardware-enforced secure boot, integrity checks, and end-to-end encrypted video as a baseline.
- Solar-powered deployment: Wire-free solar cameras reduce installation risk but the firmware attack surface must still be actively managed.
Even NDAA-compliant cameras carry risk if they share the same VLAN as corporate systems. Always isolate all IP cameras — regardless of brand — on a dedicated network segment with firewall rules restricting outbound traffic to only what is required.
Section 4
Converged Strategy: Securing Cybersecurity, Switches & Cameras Together
Physical security and IT security have converged. A compromised camera is a cybersecurity incident. A vulnerable switch is a physical security risk. Treating them separately is no longer viable — and cyber insurers and regulators increasingly agree.
Pillar 1 — Inventory and Visibility
You cannot protect what you cannot see. Maintain a continuously updated inventory of every camera, switch, and IoT device. Map connected systems, data handled, and firmware versions. Include all assets in regular risk assessments and incident response plans.
Pillar 2 — Segmentation and Access Control
Cameras and IoT devices must be on a dedicated VLAN, isolated from corporate systems. Switch admin interfaces go on a separate management VLAN, protected by MFA, accessible only via a jump server. Role-based access controls ensure only authorised personnel can modify configurations.
Pillar 3 — Continuous Monitoring and Patching
With exploitation windows now measured in days, continuous monitoring is essential. Behavioural detection tools that flag unusual API usage or unexpected outbound connections from cameras or switches are critical. Maintain log retention beyond 90 days. Apply critical firmware updates within 24–72 hours of any advisory.
Apply the same Zero Trust principles to cameras and switches that you apply to laptops — segment them, authenticate them, monitor their behaviour, and patch them on a structured schedule. If a device cannot be patched, isolate or replace it immediately.
Section 5
Your 2026 Security Action Checklist
🔐 Cybersecurity Fundamentals
- Deploy phishing-resistant MFA on all accounts — now a cyber insurance requirement
- Implement XDR or EDR with behavioural analysis — not just signature-based antivirus
- Maintain immutable, air-gapped, encrypted backups tested at least quarterly
- Apply critical patches within 72 hours of advisories
- Run tabletop ransomware exercises at least twice a year
- Audit all third-party integrations, API tokens, and service accounts quarterly
🔌 Network Switch Hardening
- Implement VLAN segmentation: Corporate, IoT/Camera, Servers, Guest, Management
- Never use default VLAN 1 for any production traffic
- Disable all unused switch ports and assign them to a quarantine VLAN
- Enable 802.1X port authentication on all access ports
- Restrict management VLAN access with MFA and full logging
- Apply switch firmware updates within 24 hours of a critical advisory
- Physically lock all switches in secured, access-controlled rooms
📷 Security Camera Hygiene
- Audit all cameras for NDAA compliance — replace banned hardware if you hold government contracts
- Isolate all IP cameras on a dedicated VLAN away from corporate systems
- Change all default usernames and passwords immediately after installation
- Apply camera firmware updates promptly — prioritise CISA KEV-listed CVEs first
- Verify cameras use encrypted communications (TLS/HTTPS) for management and streams
- Disable UPnP and any unused remote access features
- Use local NVR storage for sensitive footage instead of cloud-only solutions
Section 6
Frequently Asked Questions
What are the top cybersecurity threats in 2026?
How do I secure network switches against cyberattacks?
Are Hikvision security cameras legal to use in 2026?
What is the best NDAA-compliant security camera brand?
Should security cameras be on a separate VLAN?
What is Zero Trust and how does it apply to switches and cameras?
Conclusion
Security Is a Connected System
In 2026, the boundaries between cybersecurity, network infrastructure, and physical surveillance have dissolved. A ransomware group that gains access through a vulnerable camera VLAN can exfiltrate the same data as a nation-state actor targeting an unpatched router. Organisations that weather this landscape treat all three domains as a single, unified challenge — with consistent inventory management, network segmentation, continuous monitoring, and rapid patching across every device.
The fundamentals still work. VLAN segmentation stops lateral movement. Regular firmware updates close the most common exploitation windows. NDAA-compliant camera hardware reduces supply-chain risk. And a Zero Trust mindset applied consistently means that even when one device is compromised, attackers cannot pivot freely to your most critical assets.
For expert guidance on protecting your organisation, explore the full JazzCyberShield resource library or speak to our security team today.



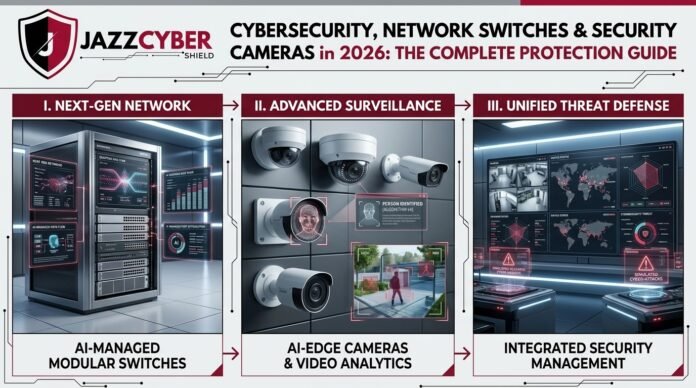
The convergence of cybersecurity, network switches, and security cameras in 2026 highlights how threats have evolved beyond traditional boundaries. It’s refreshing to see a focus on integrated solutions like AI-managed modular switches and edge surveillance — especially with rising concerns around ransomware and regulatory changes like the NDAA camera bans. This layered approach really underscores the need for a holistic view of network protection.
With the growing threat landscape, I think the combination of AI-driven network switches and cameras will make a big difference. The modular approach sounds like it will offer a lot of flexibility and adaptability in protecting against future risks.
The insight about cybersecurity in 2026 being a converged challenge rather than a single-domain problem really resonates, especially how AI-managed modular switches and edge surveillance must work in tandem. Integrating threat management directly with VLAN segmentation seems like the only viable way to counter those nation-state router exploits you mentioned. It’s clear that moving toward this layered defense model is essential for true enterprise protection.