Web3 promises true online anonymity, but are users really anonymous? While blockchain addresses are pseudonymous, your IP address can reveal metadata that links transactions to you. Therefore, true Web3 privacy requires more than a wallet.
Many Web3 users turn to VPNs for privacy. However, most centralized VPNs store logs, which poses a risk for crypto identity exposure. Even a so-called “no-log VPN” may still retain metadata. Stop server logging Web3 becomes essential for secure participation in decentralized finance, NFTs, and DAO governance.
Decentralized VPNs, or dVPNs, solve this problem. By using peer-to-peer nodes, they eliminate central logging points. This means a decentralized VPN no logs setup can protect your Web3 identity while supporting anonymous Web3 browsing.
Understanding the Risk: What Is Server Logging?
Server logging is the collection of user connection data by centralized VPNs. Traditional VPN logs typically store IP addresses, connection timestamps, and bandwidth usage. While some VPNs advertise privacy, centralized servers remain data honeypots.
These logs make users vulnerable. Hackers, regulators, or surveillance actors can access centralized server data. Even minimal logs may allow correlation between wallet activity and IP addresses. This makes web3 identity protection VPN crucial for anyone serious about privacy.
For example, a timestamp recorded by a centralized VPN could reveal when a wallet performed DeFi trades or minted NFTs. Consequently, identity exposure is possible even with pseudonymous blockchain activity. A blockchain privacy VPN or decentralized no log VPN mitigates this risk entirely.
Why Web3 Users Are Especially Vulnerable
Web3 operates on transparent blockchains. Transactions, token swaps, NFT mints, and DAO votes are public. Therefore, IP and network metadata can expose wallet owners.
Your connection to a crypto platform can leak metadata. This is particularly risky when interacting with DeFi, NFTs, or governance platforms. Additionally, analytics tools now combine IP tracking with on-chain behavior. Without a secure Web3 wallet VPN, attackers can deanonymize users.
Web3 IP address protection is crucial because metadata leaks can compromise anonymity. A dvpn for crypto privacy ensures that wallet activity and network identity remain separate, preserving your true anonymity online.
What Is a Decentralized VPN (dVPN)?
A decentralized VPN, or dVPN, is a privacy tool that replaces centralized VPN servers with a distributed network of nodes. These nodes are independent and often incentivized via blockchain tokens.
Traffic routes through multiple peer-to-peer nodes instead of a single server. Blockchain-based coordination manages authentication and payments. Encryption protects data at every step. This design ensures no central server holds logs, making it a vpn without server logs solution.
By removing central points of control, a decentralized VPN for DeFi and a crypto identity protection VPN can offer structural privacy rather than relying on corporate promises.
How Decentralized VPNs Stop Server Logging
Unlike traditional VPNs, dVPNs have no central servers. Therefore, there is no single point for storing logs.
Traffic is distributed across multiple nodes, and encryption occurs at every layer. Sessions remain ephemeral, reducing metadata retention. A web3 data privacy tool like a dVPN effectively stops server logging and prevents IP-linking attacks.
Furthermore, dVPNs operate on trustless architectures. This differs from traditional VPNs that rely on company policies. By design, private Web3 access becomes secure, and wallet-to-IP correlations are nearly impossible.
Key Security Advantages for Web3 Identity
- IP obfuscation for wallet protection – Prevents attackers from linking wallet addresses to your real location.
- Reduced correlation attack surface – Distributed routing minimizes patterns that analytics tools can track.
- Enhanced privacy for DeFi and DAO governance – Protects sensitive trades, voting, and governance activity.
- Protection against ISP tracking – Internet service providers cannot see destinations when using a web3 identity protection VPN.
- Censorship resistance – No single point of failure ensures uninterrupted access to NFT marketplaces, DAOs, and decentralized exchanges.
By combining these features, users can confidently use a decentralized VPN no logs while engaging in anonymous Web3 browsing.
dVPN vs. Traditional VPN: Side-by-Side Comparison
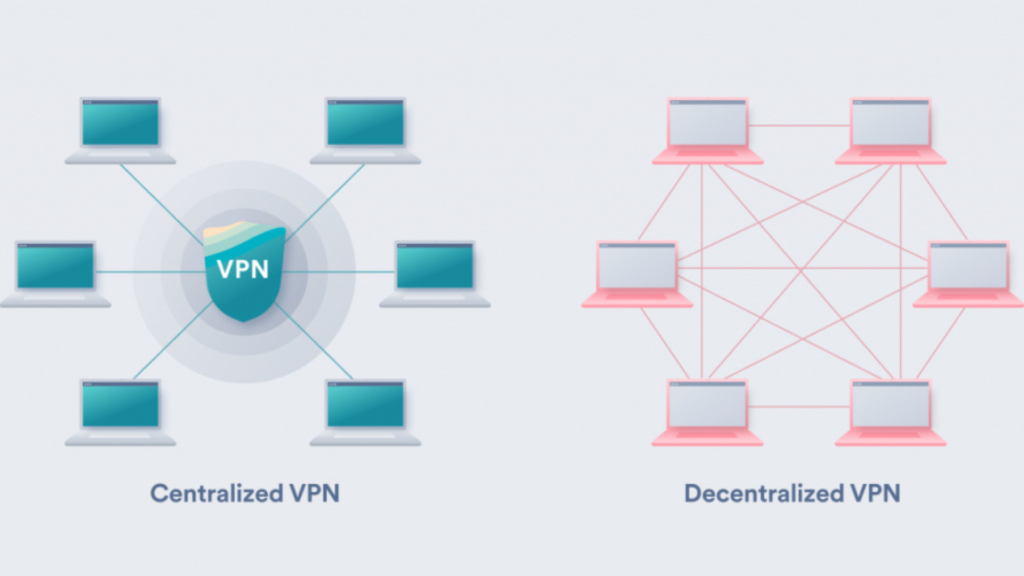
Traditional VPNs store logs and operate under centralized control. Consequently, they expose users to privacy breaches. In contrast, dVPNs distribute network control across independent nodes, making it extremely hard to collect meaningful user data.
Centralized VPNs may advertise “no-log policies,” but backend access remains. Meanwhile, no log VPN for MetaMask or a secure Web3 wallet VPN provides privacy built into the system architecture.
Additionally, centralized VPNs face legal or regulatory pressures that can force data disclosure. Decentralized networks, in contrast, resist seizure, censorship, and attacks.
Use Cases for Decentralized VPNs in Web3
- Secure DeFi trading – Protect IP metadata while swapping tokens.
- NFT minting without IP tracking – Avoid revealing your location during limited drops.
- DAO voting privacy – Ensure governance participation cannot be traced.
- Cross-border crypto access – Access DeFi platforms in restricted regions.
- Anonymous Web3 browsing – Research tokens, protocols, and NFT projects safely.
By leveraging a decentralized VPN for DeFi or a blockchain privacy VPN, users can maintain operational security while interacting across Web3 ecosystems.
Potential Limitations and Considerations
Despite strong privacy, dVPNs have trade-offs:
- Node reliability variability – Peer nodes differ in uptime and performance.
- Speed fluctuations – Distributed routing can reduce connection speeds compared to centralized VPNs.
- Token-based payments – Some dVPNs require native tokens for node incentives.
- UX challenges – Beginners may find setup and wallet integration tricky.
Even with these limits, privacy-conscious users prioritize architecture and web3 data privacy tools over convenience.
Best Practices for Maximum Web3 Privacy
- Use a decentralized VPN no logs consistently.
- Pair with a hardware wallet for cold storage.
- Avoid reusing wallet-IP combinations.
- Use privacy-focused browsers.
- Separate trading, NFT, and governance wallets.
- Practice strong operational security (OPSEC).
Together, these steps maximize protection and maintain web3 identity protection VPN standards.
The Future of Privacy: dVPNs + Web3 Infrastructure
Decentralized identity (DID) systems are emerging in 2026. By integrating dVPN networks with DIDs, users can verify credentials without revealing personal data.
Zero-knowledge proofs also enhance privacy by confirming transactions or access without sharing metadata. Combining crypto identity protection VPN with these innovations provides layered privacy.
As Web3 infrastructure grows, private Web3 access through dVPNs will become a standard requirement for secure participation.
Conclusion
Server logging is a silent threat in Web3. Even pseudonymous blockchain addresses are vulnerable when IP metadata leaks. Centralized VPNs cannot fully remove this risk.
Decentralized VPNs stop server logging by design. By distributing traffic across nodes and encrypting sessions, they protect wallets, DeFi activity, and NFT interactions.
For serious Web3 users, removing centralized trust with a decentralized no log VPN is essential. This approach ensures anonymous Web3 browsing, secure Web3 wallet VPN usage, and overall web3 data privacy tools compliance.



you are really a good webmaster. The web site loading speed is incredible.
It seems that you are doing any distinctive trick.
Also, The contents are masterwork. you have done a wonderful process on this topic!