The attackers have been using AI-Powered Cyber Attacks as a new approach to network targeting. Day by day, criminal organizations make use of machine learning cyber threats, automation hacking tools, and intelligent malware attacks. Thus, it becomes very necessary for the organizations to very quickly upgrade their defenses. Furthermore, the network protection strategies of today require advanced tools such as next-generation firewalls, AI firewall detection, and real-time threat analytics. Security teams then have no option but to comprehend how firewalls detect these threats. We are going to examine in this article, the triumph of firewalls against the AI-Powered Cyber Attacks in the contemporary networks.
What are AI-Powered Cyber Attacks?
AI-Powered Cyber Attacks make use of artificial intelligence in the field of cyber security to quickly get the better of the system. Besides that, the attacker performs the scan automatically, changes the load, and avoids the conventional defenses. On top of that, these attacks are constantly learning from their failures and instantly altering patterns. Thus, the basic signature detection in most cases becomes ineffective. Rather, the threats necessitate a mix of behavior-based threat detection, machine learning network monitoring, and anomaly detection systems. Consequently, the modern firewalls have to be more alert to detect the unusual activities.
Presently, the intruders are employing self-learning malware that is able to go undetected due to blending with regular traffic. Besides that, AI tools are employed to observe the network behavior and impersonate legitimate users. Therefore, firewalls will have to rely on behavioral analytics and context-aware threat detection. Thus, it is very important to have a clear understanding of how the attackers operate. In fact, security teams now perceive that AI-powered threat behavior is the greatest risk in the area of cybersecurity.
The Reasons Why Traditional Firewalls Can’t Handle Modern Threats
Firewalls of the olden days believed in signature-based detection and thus, banned the malware that was already known. But the AI-Powered Cyber Attacks have been and will be evolving every day. Hence, unchanging barriers are no more a means to stop the unknown threats. In addition, the traffic that is encrypted does not let the code of the bad guys pass through. Furthermore, the hybrid cloud systems have made the flow of data more complicated. It is because of all these factors that the signature systems are falling short one after the other. So, companies should switch to AI-driven firewall security that not only analyzes the behavior of the signature but also that of itself.
In addition, attackers exploit zero-day automation in order to nullify the old rules. Otherwise, you would have a hard time finding the attackers through the malicious bots that are continuously changing according to the situation. For example, they are fast, they cover large areas and they are good at avoiding pattern matching. Thus, the enterprises are experiencing more breaches than ever. In today’s world a defense system with real-time threat detection, network behavior analysis, and intrusion prevention systems needs to be combined in one solution.
Next-Generation Firewalls: A New Defense Standard
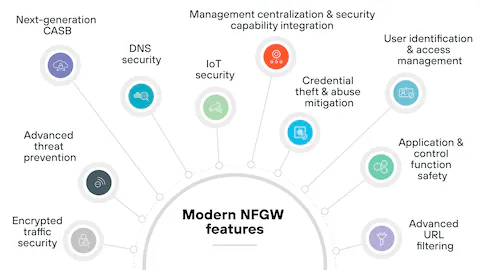
NGFW or Next-Generation Firewalls are the ones that provide enhanced visibility of the entire traffic. They go to the extent of inspecting packets at each and every layer. Moreover, NGFWs use machine learning for threat detection to spot weird behavior. Because of this, they can block AI-Powered Cyber Attacks that are trying to sneak into the common applications. Also, NGFWs ensure monitoring of the traffic that is encrypted without the networks being slowed down.
These systems provide a combination of real-time analytics, application awareness, and user identity tracking. Consequently, firewalls are able to detect threats faster and in a smarter way. On the other hand, they continue to prevent the attacks that try to behave like normal users. Thus, NGFWs have become a must-have in the modern cyber defense strategies.
Firewalls Enhanced by Machine Learning and Behavioral Analytics
The employment of machine learning in the firewall systems enables them to recognize and learn the usual network patterns. It assists the systems in spotting any anomaly at a quicker pace. A good example would be when a machine suddenly makes a large data transfer; machine learning will signal it immediately. Moreover, besides performing preventive measures, a forward-looking firewall carries out predictive modeling to finish threat detection before any harm is done. Thus, the AI-based firewalls using the threat intelligence are able to decrease the chances to an extent that is far beyond what the regular systems can do.
In the same way, behavioral analytics reveals the tiniest shifts in network traffic that may indicate unauthorized access. Besides, machine learning acts as a filter for false alarms preventing unnecessary alerting of security personnel, thus encouraging better working conditions. Hence, organizations reach a quicker incident response, less downtime, and better resistance against the use of malware that is automatically operated.
Threat Intelligence and Firewall Automation in Real-Time
Firewalls of the present day are equipped with real-time threat intelligence in order to be aware of the latest risks. Besides, they carry out the process of threat data collection worldwide and apply it immediately. Consequently, the firewalls get rid of the attacks that might be the case anywhere around the globe. Moreover, automation facilitates the firewalls in modifying the rules seamlessly.
Additionally, the automated reaction decision leads to a tiny error margin occurring due to human intervention. Also, the firewalls are implementing the automated threat containment tactics that allow them to terminate the sessions regarded as suspicious on the spot. This is a reason, businesses are able to secure their sensitive resources even in the case of large attack sieges.
Network Anomaly Detection and Context Awareness
Firewalls work in conjunction with network anomaly detection to point out everything that is not normal. Besides, it is monitoring the flow of traffic constantly. Moreover, it assesses the current activity against the already established standards. As a result, the anomalies are alerted pretty quickly. Thus, the firewalls can stop the sneaky threats that are masking themselves in the normal traffic. Moreover, the context awareness facilitates the firewalls in being acquainted with the users, devices, and applications.
Protecting Cloud and Remote Work Environments
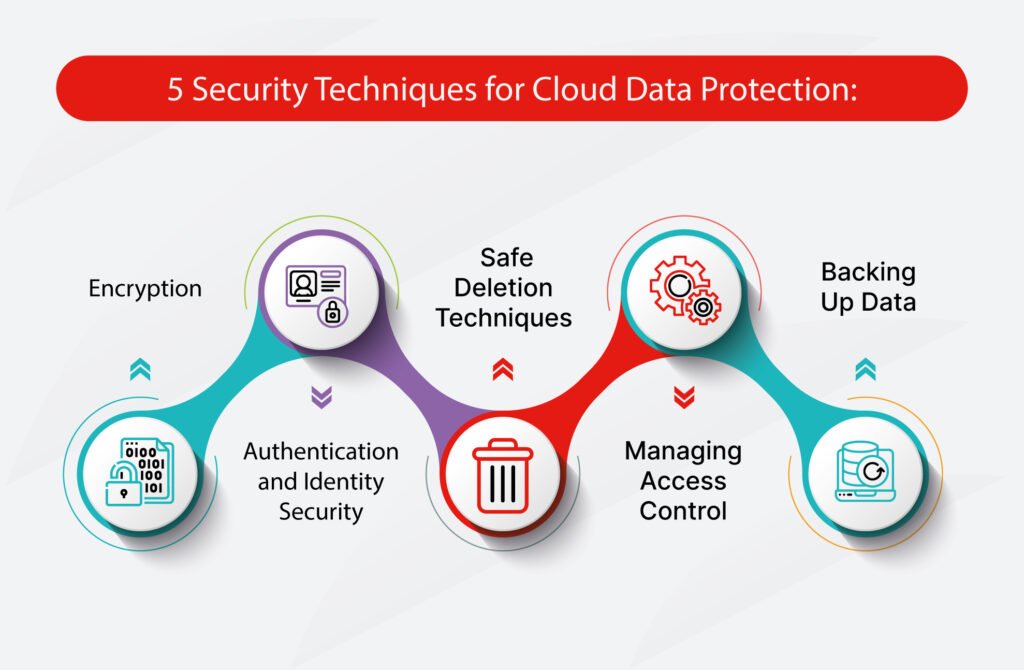
The modern environments are comprised of cloud networks and remote users. Hence, the firewalls have to protect the traffic not only between clouds and users but also among various systems. Additionally, the cloud networks are a source of unique security issues since the infrastructure is constantly changing. Therefore, cloud firewall security has become a part of modern defense strategy. Also, AI firewalls are capable of adjusting to the dynamic workloads and unpredictable traffic.
The challenge of remote work is that it opens the door wider to the attackers. Due to the diversity of endpoints, the attackers have many more routes to breach the system. Hence, firewalls have to simultaneously take care of endpoint protection, remote access security, and VPN security. Through AI analytics, contemporary firewalls have surpassed legacy tools in terms of security in such environments.
Zero Trust Security and AI Firewalls
The Zero Trust Security Model presupposes that no user is secure until the opposite is demonstrated. In addition to that, the must authenticate each connection request. As a result, Zero Trust necessitates constant verification and inspection. Hence, firewalls apply AI firewall logic in order to maintain strict access control.
Besides, Zero Trust is compatible with behavioral analytics and this turns up the possibility to detect insider threats. Moreover, this method simplifies the detection of AI-Powered Cyber Attacks, as it becomes evident through the deviance from the standard behavior. Presently, Zero Trust is considered to be one of the most important elements in the enterprise’s strong cybersecurity.
Future of AI in Firewall Technology
The future of firewall technology equals to fully automatic defense systems taking their cue from AI. Apart from that, the firewalls would be functioning with very little human input. Furthermore, predictive analytics would be giving the heads up about the threats even before they happen. Thus, making the networks more attack-resistant even to the extent of large-scale ones.
Not only that, firewalls will back up the endpoints, cloud security tools and security orchestration platforms even more. Consequently, organizations will enjoy quicker threat response and improved data safeguarding.
Conclusion
To sum up, AI-Powered Cyber Attacks will dominate the scene of cybercrimes in the future. Consequently, no contemporary network can exist without cutting-edge firewalls. Besides, the modern defense is based on next-gen firewalls, machine learning, threat detection, behavioral analytics, and real-time threat intelligence. Thus, it is high time for the organizations to take the necessary steps to protect their assets and data. Also, incorporating advanced firewall solutions means getting a layer of protection against smart and automated threats. Simply put, firewalls have transformed from being mere barriers to being savvy defenders in the AI-Powered Cyber Attacks landscape.
FAQs: AI-Powered Cyber Attacks & Firewall Security
What are AI-Powered Cyber Attacks?
AI-Powered Cyber Attacks are the types of threats that use artificial intelligence and machine learning and thus, can perform all the activities related to hacking automatically, modify attack patterns and break through traditional security systems. These attacks are constantly changing and adapting to the environment while modern networks are more prone to these types of threats than to manual ones.
How do firewalls detect AI-Powered Cyber Attacks?
Firewalls make detection of AI-Powered Cyber Attacks through a combination of machine learning threat detection, behavioral analytics, and real-time threat intelligence. Their analysis of the traffic uses behavioral methods rather than solely relying on known signatures.
Can firewalls be a shield for cloud and remote work setups?
Certainly, the security of the cloud firewall and the detection by AI firewalls are invincible for both the cloud and the remote users. In fact, all those firewalls are very good at becoming accustomed to the changing nature of traffic and at securing distributed environments.
What is meant by Zero Trust security and what is the role of firewalls in it?
Zero Trust security continuously authenticates every user and device. Firewalls are the ones that impose this model by relying on AI for access control, monitoring behavior and conducting inspections non-stop.
What is the reason for the significance of real-time threat detection?
Real-time threat detection has the capacity to halt the attacks immediately. Because AI-Powered Cyber Attacks are quick, the combined automated and real-time firewall responses can save data from breaches and systems from damage.
Are AI firewalls a necessity for cybersecurity in enterprises?
Absolutely, AI-based firewall protection is a must for large businesses as it helps them to stand up against the whole range of modern threats. In addition, those firewalls have the capability of scaling up easily, cutting down on response time, and keeping the most sensitive business data safe.



