A dangerous new xlabs_v1 botnet has emerged in May 2026, and it is already hijacking thousands of internet-exposed IoT devices across the globe. Security researchers at Hunt.io discovered this Mirai-derived malware after stumbling on an unsecured Netherlands-hosted server that contained the entire attack toolkit. If you run security cameras, smart TVs, Android-based devices, or even a basic home router, your network could already be on the target list.
The xlabs_v1 botnet is not just another script-kiddie clone of Mirai. It packs 21 different flood attack variants, supports multiple processor architectures, and is being sold as a DDoS-for-hire service to attackers who want to take down game servers, Minecraft hosts, and small business websites. In this guide, we break down exactly how the threat works and the seven defenses every IT manager, network engineer, and small business owner needs to deploy this week.
Quick takeaway: The xlabs_v1 botnet exploits Android Debug Bridge (ADB) on TCP port 5555. If your IoT devices have ADB enabled, they are at risk. Disable it, segment your network, and put a proper firewall in front of your devices today.
Table of Contents
What Is the xlabs_v1 Botnet?
The xlabs_v1 botnet is a newly identified Mirai-derived malware family that recruits compromised IoT and Android-based hardware into a distributed network capable of launching massive denial-of-service attacks. Hunt.io researchers found the operation hiding behind the IP address 176.65.139[.]44, where the threat actor (operating under the alias “Tadashi”) had carelessly left an unauthenticated directory exposed on the public internet.
What sets this malware apart from typical Mirai forks is its commercial polish. Rather than being a hobby project, the xlabs_v1 botnet is offered as a paid DDoS-for-hire service, with bandwidth-tiered pricing and 21 different flood variants spanning TCP, UDP, and raw network protocols. Some of these variants — including RakNet floods and OpenVPN-shaped UDP — are specifically engineered to slip past consumer-grade DDoS protection.
In simple terms, this is not amateur work. It is a mid-tier criminal product designed to be reliable, fast, and affordable for anyone who wants to knock a competitor offline.
How the xlabs_v1 Botnet Hijacks IoT Devices
Understanding the infection chain helps you block it. The xlabs_v1 botnet follows a methodical, repeatable pattern that abuses one specific weakness most consumers do not even know exists on their devices.
The Android Debug Bridge (ADB) Exploit
The primary infection vector is Android Debug Bridge (ADB) running on TCP port 5555. ADB is a developer tool that ships enabled by default on many cheap Android TV boxes, set-top boxes, smart TVs, and IoT devices. When ADB is exposed to the internet without authentication, anyone on the global network can push commands directly to that device.
The attacker scans for open port 5555, connects, and pushes a single shell one-liner that downloads and executes architecture-specific payloads. Once inside, the malware drops a malicious APK into the /data/local/tmp directory and gains persistent control.
Multi-Architecture Targeting
Unlike older botnets that focused on one chipset, the xlabs_v1 botnet ships with multi-architecture builds covering:
- ARM — used in most smart cameras, routers, and smart TVs
- MIPS — common in older home routers and embedded devices
- x86-64 — found in Android TV boxes and set-top devices
- ARC — used in IoT-grade chipsets
- Android APK — for direct mobile and TV device infection
This wide compatibility means almost every internet-exposed device with ADB enabled is fair game — from a $30 Android TV stick to a small office security camera.
After installation, the bot opens 8,192 simultaneous TCP sockets to profile the victim’s bandwidth, reports the result back to a control panel, and the operator assigns a price tier. The malware then waits for paid attack commands while quietly killing rival botnets that might be sharing the same victim.
Why xlabs_v1 Is More Dangerous Than Past Mirai Variants
Older Mirai variants were noisy, easy to detect, and limited in scope. The xlabs_v1 botnet improves on every weakness:
- Stealth resolution. It uses OpenNIC for command-and-control resolution and falls back to a firewall-punching SOCKS-style listener on TCP port 26721 when blocked.
- Process masking. The binary disguises itself as
/bin/bashto evade casual inspection on Linux-based IoT firmware. - Competitor elimination. A “killer” subsystem scans
/proc, terminates rival botnet processes, and removes competing malware from port 24936 to monopolize victim bandwidth. - Anti-fingerprinting payloads. RakNet and OpenVPN-shaped UDP floods specifically target gaming infrastructure and bypass cheap scrubbing services.
For small and medium businesses running cameras, VoIP phones, or unsecured routers, this means infection can happen silently — and your bandwidth could be powering attacks on someone else for weeks before you notice.
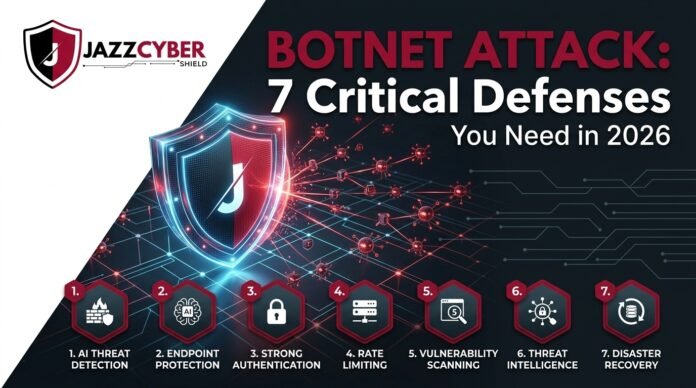
7 Critical Defenses Against the xlabs_v1 Botnet
Here is the action plan every IT manager, MSP, and SMB owner should execute this week to stop the xlabs_v1 botnet at the gate.
1. Disable Android Debug Bridge on All Production Devices
ADB should never be reachable from the internet. Audit every Android TV box, set-top box, smart display, and Android-based camera on your network. Open Settings → Developer Options and turn ADB off. If the device cannot disable ADB, assume it is compromised and replace it with hardened enterprise hardware.
2. Deploy a Next-Generation Firewall at Your Network Edge
A consumer router will not stop a determined botnet. You need a next-generation firewall (NGFW) with intrusion prevention, application control, and outbound traffic filtering. Brands like Fortinet, SonicWall, and WatchGuard are purpose-built for exactly this scenario, and they automatically block known botnet command-and-control infrastructure through threat intelligence feeds. Browse our full range of enterprise firewalls and security appliances to lock down your perimeter.
3. Segment IoT Devices Onto Isolated VLANs
Network segmentation is the single most effective control against botnet lateral movement. Place every IoT device — cameras, smart TVs, sensors, printers — onto a dedicated VLAN with strict outbound rules that allow traffic only to the specific destinations each device legitimately needs. We covered the practical setup steps in our guide on VLAN home networking and IoT isolation, which walks you through the full configuration.
4. Replace Default IoT Credentials Immediately
The xlabs_v1 botnet family historically thrives on default credentials. Every IP camera, NVR, router, and smart device must have its factory password rotated to a long, unique passphrase. Better yet, deploy certificate-based authentication where the hardware supports it.
5. Monitor Outbound Traffic for Anomalies
The botnet’s bandwidth-profiling routine opens 8,192 parallel TCP sockets — a behavior that is impossible to miss if you are watching. Configure your firewall, switch, or SIEM to flag any IoT device that suddenly opens hundreds of outbound connections. This single rule provides early warning even before signature-based detection catches the malware.
6. Use DDoS-Protected Infrastructure for Public Services
If you host websites, game servers, or APIs, do not rely on consumer-grade protection. Sign up for a CDN with built-in DDoS mitigation such as Cloudflare or Akamai Prolexic, and put your origin servers behind enterprise firewalls that can absorb volumetric floods.
7. Patch Firmware Religiously and Replace End-of-Life Hardware
The cheapest, most overlooked defense is firmware updates. Set a recurring monthly task to check every router, camera, switch, and access point for vendor firmware releases. Devices that no longer receive security updates must be retired — they are tomorrow’s botnet recruits.
Industries Most at Risk From the xlabs_v1 Botnet
Based on the malware’s targeting and the Hunt.io infrastructure analysis, these sectors should treat this as a top-priority threat:
- Gaming and Minecraft hosting providers — explicit primary targets of the DDoS service
- Small e-commerce stores — used as test targets and extortion victims
- Schools and universities — large IoT footprints with weak segmentation
- Healthcare clinics — connected medical devices and IP cameras
- Retail with surveillance systems — cheap rebadged cameras with default ADB
- Residential ISPs — millions of subscriber routers form the easiest victim pool
If you sell, install, or manage networks for any of these verticals, treat the xlabs_v1 botnet as your number-one operational risk for Q2 2026.
Final Verdict on the xlabs_v1 Botnet Threat
The xlabs_v1 botnet is a clear signal that the IoT threat landscape has matured into a commercial criminal economy. Attackers no longer need elite skills — they just need a credit card and a target. For defenders, that means the bar for “good enough” security has been raised again. Disabling ADB, segmenting IoT, and putting a real firewall between your network and the internet are no longer optional.
The good news is that every defense in this guide is achievable this week, and most are achievable today. Start with the firewall and the VLAN — those two controls alone neutralize roughly 80 percent of the xlabs_v1 botnet infection surface. Then build out the rest of the playbook over the following sprint.
If you need help selecting the right firewall, switch, or camera replacement for your environment, our team at Jazz Cyber Shield specializes in exactly this kind of hardening project. Get in touch through our contact page and we will scope a defense package that fits your network and your budget.
Frequently Asked Questions About the xlabs_v1 Botnet
Q1. What is the xlabs_v1 botnet? The xlabs_v1 botnet is a Mirai-derived malware family discovered in May 2026 that hijacks IoT devices through exposed Android Debug Bridge services to launch DDoS-for-hire attacks.
Q2. How does the xlabs_v1 botnet infect devices? It scans the internet for open TCP port 5555 (Android Debug Bridge), connects without authentication, and pushes architecture-specific malware payloads that grant the attacker persistent control.
Q3. Which devices are most at risk from the xlabs_v1 botnet? Android TV boxes, set-top boxes, smart TVs, cheap IP cameras, residential routers, and any IoT-grade hardware shipping with ADB enabled by default are the primary targets.
Q4. Can a normal home router block the xlabs_v1 botnet? Most consumer routers cannot reliably stop modern botnet command-and-control traffic. A next-generation firewall with threat intelligence feeds is the recommended defense.
Q5. How do I know if my network is already infected? Watch for IoT devices opening hundreds or thousands of simultaneous outbound TCP connections, unexpected bandwidth spikes, and processes masquerading as /bin/bash on embedded Linux firmware.