SonicWall and Fortinet firewall attacks have officially become the #1 cybersecurity threat of 2026. According to Barracuda’s SOC Threat Radar report released in April 2026, brute-force authentication attempts targeting SonicWall and FortiGate devices accounted for over 56% of all confirmed security incidents between February and March 2026. If you operate a business firewall right now, the attackers are already scanning your IP.
The numbers are staggering. GreyNoise documented 84,142 scanning sessions from 4,305 unique IP addresses hitting SonicWall devices in just four days. Meanwhile, Fortinet customers are battling an actively exploited zero-day, CVE-2026-24858, that lets attackers bypass FortiCloud SSO authentication and create rogue admin accounts on FortiGate firewalls.
This guide breaks down exactly why SonicWall and Fortinet firewall attacks have exploded, which CVEs are being weaponized right now, how to detect compromise, and what every IT leader must do this week to stay protected.
Table of Contents
Why SonicWall and Fortinet Firewall Attacks Are Surging in 2026
Edge security devices sit at the perimeter of every business network — which is exactly why they have become the preferred entry point for ransomware gangs and state-sponsored attackers. The SonicWall and Fortinet firewall attacks we’re seeing in 2026 didn’t appear out of nowhere; they are the natural escalation of a multi-year trend.
Here’s what the latest threat intelligence reveals:
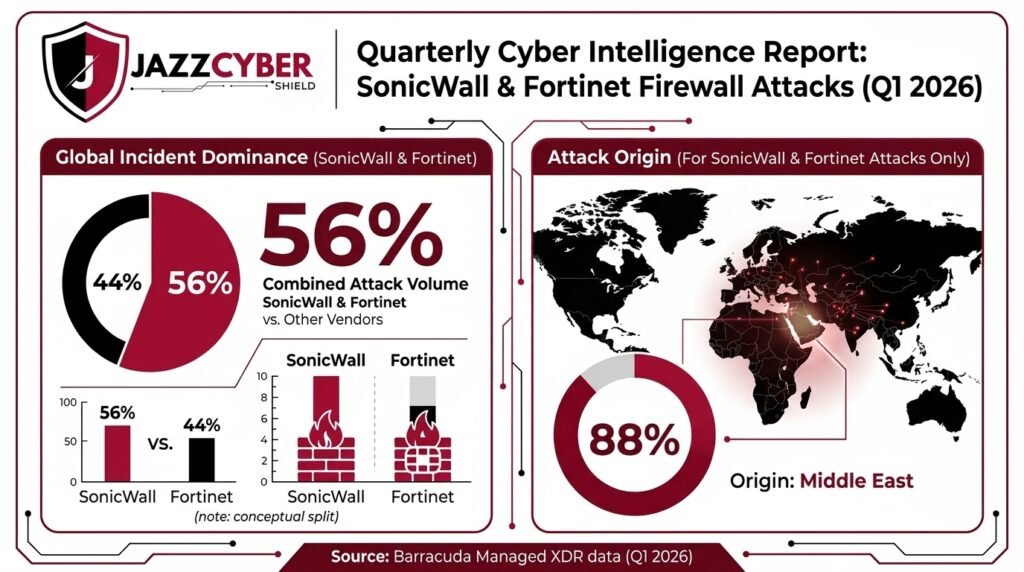
- 56% incident dominance: Barracuda Managed XDR confirmed that brute-force attempts on SonicWall and FortiGate devices made up the majority of all confirmed Q1 2026 incidents.
- 88% from the Middle East: The vast majority of the malicious traffic originated from one geographic cluster, indicating coordinated infrastructure.
- 430,000+ exposed devices: Over 430,000 SonicWall firewalls remain publicly accessible on the internet, with tens of thousands still running vulnerable or end-of-life firmware.
- 10,000 vulnerable Fortinet instances: Shadowserver scans identified nearly 10,000 Fortinet devices with FortiCloud SSO enabled, roughly 25% of them based in the United States.
- 8x increase in edge exploitation: The 2025 Verizon Data Breach Investigations Report documented an eightfold rise in attacks targeting VPNs and edge appliances compared to prior years.
The pattern is unmistakable. Attackers no longer waste time on phishing campaigns when a single weak SSL VPN password can hand them the entire corporate network. To understand the full threat picture, read our deep dive on the top cybersecurity threats in 2026.
The Real Reason Hackers Target SonicWall and Fortinet Devices
Edge firewalls are uniquely valuable to attackers for three reasons. First, they sit outside the network and accept traffic from anywhere on the internet. Second, they often hold privileged credentials and VPN tunnels into trusted internal segments. Third — and most critically — they are blind spots: you cannot install endpoint detection and response (EDR) software on a firewall.
That blind spot is exactly what ransomware affiliates like Akira have weaponized throughout 2025 and 2026. Once attackers get a foothold via SonicWall SSL VPN or FortiGate SSO, they typically:
- Export the entire firewall configuration, including hashed credentials
- Create persistent rogue administrator accounts
- Modify VPN settings to grant ongoing access
- Pivot laterally into Active Directory and file servers
- Disable backup systems before deploying ransomware
The interval between initial SSL VPN access and full ransomware encryption is now often less than 24 hours. If your business hasn’t invested in a next-generation firewall (NGFW) with proper hardening, you are operating on borrowed time.
The 5 Critical Vulnerabilities Behind 2026’s Firewall Attacks
Not all SonicWall and Fortinet firewall attacks exploit the same weakness. Here are the five CVEs currently driving the bulk of the damage:
1. CVE-2026-24858 — Fortinet FortiCloud SSO Bypass (CVSS 9.3)
Disclosed in late January 2026, this authentication bypass lets an attacker with any valid FortiCloud account log into FortiGate, FortiManager, FortiAnalyzer, FortiProxy, and FortiWeb devices registered to other organizations. CISA added it to the Known Exploited Vulnerabilities catalog on January 28, 2026. Patches are available in FortiOS 7.4.11 and later.
2. CVE-2024-40766 — SonicWall SonicOS Improper Access Control (CVSS 9.3)
Originally disclosed in August 2024, this flaw is still being exploited by the Akira ransomware group. It primarily affects Gen 6 and Gen 7 SonicWall firewalls, especially those that migrated configurations without resetting local user passwords. Patched in SonicOS 7.3.0+.
3. CVE-2024-53704 — SonicWall SSL VPN Auth Bypass (CVSS 9.8)
This authentication bypass allows an unauthenticated attacker to disclose private information, terminate active VPN sessions, and bypass MFA entirely. Public proof-of-concept exploits are now widely available, dramatically lowering the bar for attack.
4. CVE-2025-59718 / CVE-2025-59719 — Fortinet SAML SSO Bypass
This pair of late-2025 vulnerabilities allowed unauthenticated SSO bypass via crafted SAML messages on FortiOS, FortiWeb, FortiProxy, and FortiSwitchManager. Although patched, the related CVE-2026-24858 reveals the patches were incomplete.
5. CVE-2020-12812 — Five-Year-Old Fortinet 2FA Bypass
Incredibly, this 2020 vulnerability is back in active exploitation in 2026. Attackers bypass two-factor authentication by simply changing the case of the username (e.g., “JSmith” instead of “jsmith”). APT5, Iranian-backed actors, and Russian SVR groups have all been observed exploiting it. As of January 2026, over 10,000 Fortinet firewalls remain unpatched globally.
How to Detect SonicWall and Fortinet Firewall Attacks on Your Network
Early detection is the difference between a contained incident and a full-blown ransomware disaster. Watch for these specific indicators of compromise (IOCs):
- Unfamiliar administrator accounts: Generic names like “cloud-init@mail.io,” “admin2,” or accounts you didn’t create are a major red flag.
- HTTP/1.0 requests with modern browser user agents: Roughly 70% of malicious SonicWall scanning traffic uses a Chrome-on-Linux user agent paired with HTTP/1.0 — an unusual combination.
- SSL VPN logins from hosting provider IPs: Logins originating from The Constant Company, BL Networks, or Kaopu Cloud HK indicate likely compromise.
- Configuration export events: Sudden full-configuration exports from your FortiGate or SonicWall web interface suggest credential theft is underway.
- VPN tunnel modifications: Watch for new VPN policies granting access to accounts you don’t recognize.
- Failed login spikes: A sudden surge in failed authentication attempts often precedes successful brute-force breaches.
If you don’t already have continuous monitoring in place, our guide on how to monitor all devices on your network in real time walks through free tools you can deploy today.
10-Step Action Plan to Stop SonicWall and Fortinet Firewall Attacks Right Now
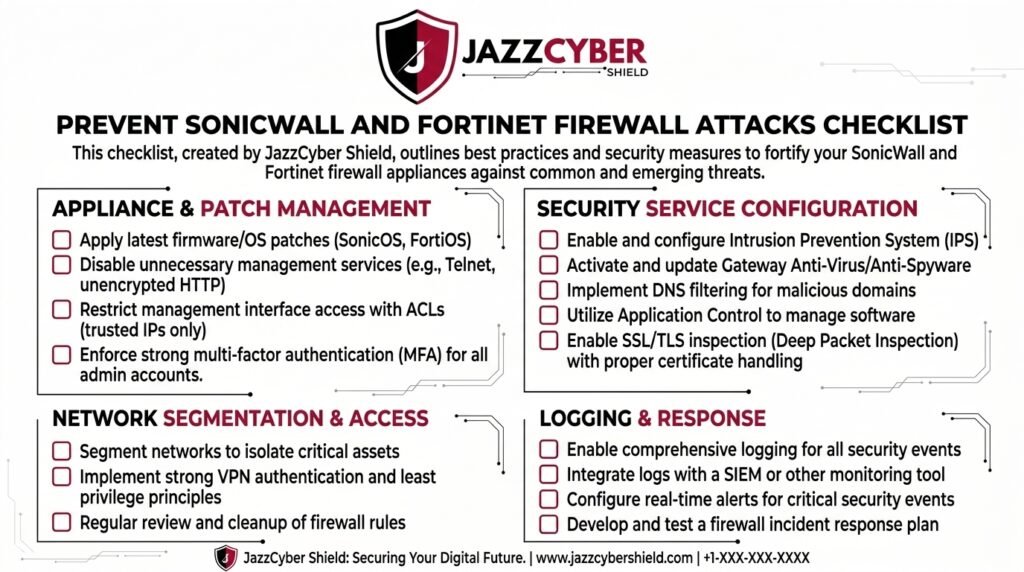
Whether you’re running a SonicWall TZ series, a FortiGate 60F, or anything in between, the following hardening checklist will close most of the attack vectors driving 2026’s firewall breaches:
- Patch immediately. Upgrade SonicWall firewalls to SonicOS 7.3.0 or later. Upgrade FortiGate to FortiOS 7.4.11 or later.
- Reset every local user password. Especially for accounts migrated from older firmware (Gen 6 to Gen 7 SonicWall migrations are the most exposed).
- Enforce multi-factor authentication. Mandatory MFA on all SSL VPN, admin, and SSO accounts — no exceptions.
- Restrict management interface access. Allow administrative login only from trusted internal IP ranges using local-in policies.
- Disable FortiCloud SSO if unused. Navigate to System → Settings → “Allow administrative login using FortiCloud SSO” → Off.
- Enable Botnet Protection and Geo-IP Filtering. Block traffic from regions where you have no legitimate business activity.
- Remove inactive accounts. Audit user lists monthly and decommission anything dormant for 30+ days.
- Disable SSL VPN if not required. If your team works on-site or uses a different remote access method, turn SSL VPN off entirely.
- Monitor logs continuously. Forward firewall logs to a SIEM or managed XDR platform for real-time anomaly detection.
- Replace end-of-life hardware. If your device runs unsupported firmware, no amount of hardening will save it. Browse current-gen options at our enterprise firewall collection.
Best Replacement Firewalls in 2026 (For Businesses Switching Now)
If your existing SonicWall or Fortinet device is end-of-life, unpatchable, or you simply want a fresh, hardened deployment, these are the most-recommended models for 2026 from authorized USA distribution:
Fortinet FortiGate Series (Latest FortiOS 7.4.11+)
For businesses staying with Fortinet, the current generation FortiGate appliances deliver SD-WAN, IPS, and AI-powered threat detection in a single box. Browse current models in our authorized Fortinet store.
SonicWall TZ and NSa Series (SonicOS 7.3+)
SonicWall’s latest TZ and NSa firewalls ship with hardened brute-force resistance and improved MFA controls. See current authorized inventory at our SonicWall firewall store.
WatchGuard Firebox Series (Alternative Vendor)
If you’ve lost trust in SonicWall and Fortinet entirely, WatchGuard Firebox appliances are a strong third-vendor alternative — particularly the M-series for SMB deployments. Explore options on our WatchGuard firewall page.
Are SonicWall and Fortinet Still Safe in 2026? Honest Verdict
Yes — but only if you operate them correctly. The vendors aren’t the problem. Unpatched firmware, weak passwords, exposed management interfaces, and migrated-but-not-reset accounts are the problem. Both SonicWall and Fortinet have invested heavily in security improvements through 2025 and 2026, and their current-generation firmware is markedly harder to attack.
The businesses getting breached are not running modern, hardened deployments. They’re running aging firewalls with default configurations, no MFA, and management portals exposed to the open internet. If your firewall falls into that category, the question isn’t whether you’ll be attacked — it’s when. For a deeper look at why preparation matters, see our analysis of why 60% of small businesses close within 6 months of a cyberattack.
Frequently Asked Questions About SonicWall and Fortinet Firewall Attacks
What is causing the spike in SonicWall and Fortinet firewall attacks in 2026?
The spike is driven by a combination of newly disclosed CVEs (such as CVE-2026-24858), unresolved legacy vulnerabilities (CVE-2024-40766), publicly available proof-of-concept exploits, and coordinated brute-force campaigns originating largely from the Middle East. Edge firewalls are now the #1 ransomware initial access vector.
Should I disable SSL VPN on my SonicWall or FortiGate firewall?
If you can operate without SSL VPN, yes — disable it temporarily until your firmware is fully patched and MFA is enforced. SSL VPN is the single most-targeted feature on both vendors’ devices in 2026.
How do I know if my firewall has already been compromised?
Check for unfamiliar administrator accounts, unexplained VPN policy changes, configuration export events in your logs, and successful logins from hosting-provider IP ranges. Any of these are strong indicators of compromise.
Is multi-factor authentication enough to stop these attacks?
MFA blocks the majority of brute-force attempts, but it is not foolproof. CVE-2024-53704 specifically allows MFA bypass on vulnerable SonicWall versions, and CVE-2020-12812 bypasses 2FA on FortiOS by exploiting username case sensitivity. MFA is necessary but must be combined with patched firmware and restricted management interfaces.
Are SonicWall and Fortinet still recommended in 2026?
Yes, both vendors remain industry leaders when their devices are properly patched, hardened, and monitored. The vulnerabilities are real, but the alternative — running an unmonitored network without enterprise-grade firewalling — carries far greater risk.
Final Word: Don’t Wait for the Breach
The data from Barracuda, GreyNoise, Arctic Wolf, and CISA all point to the same conclusion: SonicWall and Fortinet firewall attacks are not slowing down. They are accelerating, automating, and increasingly hard to detect. The window between scanning and exploitation is now measured in days, not months.
If your firewall is overdue for replacement, running unsupported firmware, or simply hasn’t been audited in over a year, take action this week. Browse hardened, authorized-distribution firewalls at the Jazz Cyber Shield firewall store, or contact our IT security team for a free hardware compatibility check. The cost of preparation is always lower than the cost of recovery.