Online privacy has never mattered more. With surveillance capitalism at an all-time high and cybersecurity threats evolving rapidly, millions of Americans are re-evaluating how they protect their internet connections. Traditional V P Ns have long been the go-to tool — but a new category is gaining ground: the decentralized VPN (d V P N). Built on block chain technology and powered by peer-to-peer networks, dVPNs promise a fundamentally different — and potentially stronger — approach to privacy.
In this comprehensive guide, we break down everything you need to know about decentralized VPNs, compare the top options, and answer the most critical question: is a dVPN actually better than a regular VPN for US users in 2025?
Table of Contents
1. What Is a Decentralized VPN (dVPN)?
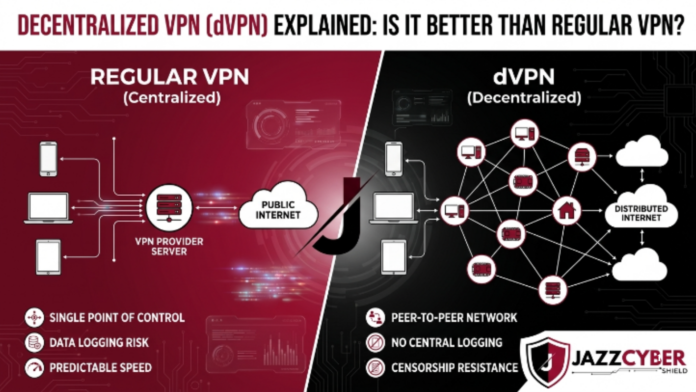
A decentralized VPN, often called a dVPN, is a privacy network that routes your internet traffic through a distributed, peer-to-peer system rather than through servers owned by a single company. In contrast to traditional VPN providers—which operate centralized server farms and ask you to trust their no-logs policies—a blockchain VPN or Web3 VPN completely removes the central authority. Consequently, users gain greater control over their privacy and security.
In a d V P N, everyday users around the world share their unused bandwidth as “nodes.” When you connect, one or more volunteer nodes route your traffic, ensuring that no single entity controls or monitors your connection. Open-source code governs the system, and in most cases, a blockchain-based token economy incentivizes participation
Key Definition: A decentralized VPN is a peer-to-peer privacy network with no central server, no single company in control, and — in the best implementations — no ability for anyone to maintain user logs, even if legally compelled.
The concept aligns closely with the broader Web3 movement: trustless, permissionless, and community-owned infrastructure replacing corporate middlemen. Projects like Mysterium Network and Orchid VPN are the most prominent examples available to US users today.
2. How Does a Decentralized VPN Work?
Understanding how a decentralized VPN works requires looking at three interlocking components: the node network, the routing protocol, and the token incentive model.
The Node Network (Peer-to-Peer Architecture)
A peer-to-peer VPN is built from thousands of individual nodes — computers or devices operated by regular users. When you install a dVPN app, you can choose to become a node yourself. One of these nodes encrypts your traffic and routes it, just like a VPN server would—except this ‘server’ runs on someone’s home computer in Chicago or a rented VPS in Texas.
Blockchain-Based Trust & Payments
Because there’s no central authority, dVPNs use blockchain technology to handle trust and payments. Smart contracts automatically manage node payments, uptime verification, and service quality. When you use bandwidth, you pay in cryptocurrency tokens — typically the network’s native token. The dVPN token incentive model rewards nodes financially for providing honest, high-quality service, aligning economic interests without relying on centralized control.
dVPN Privacy: No Logs by Architecture
The most compelling privacy argument for dVPNs is structural. First, a traditional VPN company promises not to keep logs. However, a dVPN, by design, makes it technically difficult or impossible to collect logs centrally. Moreover, the node operator sees only encrypted traffic passing through. Additionally, they cannot read its contents. Therefore, there is no corporate headquarters to receive a government subpoena demanding user records.
dVPN Privacy Explained: The decentralized VPN no-logs policy isn’t a marketing promise — it’s an architectural reality. No central database, no central logs, no single point of legal compulsion.
For further reading on how block chain enhances privacy, see this detailed overview from the Electronic Frontier Foundation (EFF), one of the most authoritative voices on digital privacy in the US.
3. Decentralized VPN vs Traditional VPN: Full Comparison
The dVPN vs traditional VPN debate comes down to trust, speed, ease of use, and your specific threat model. Furthermore, price structures are radically different. Here is a comprehensive breakdown:
| Feature | Decentralized VPN (dVPN) | Traditional VPN (e.g., NordVPN) |
| Server Control | Community nodes | Centralized company servers |
| No-Logs Policy | Structural (by architecture) | Policy-based (trust required) |
| Speed | Often slower, variable | Faster, consistent |
| Censorship Bypass | Excellent (hard to block) | Good, but IPs can be blocklisted |
| Payment Method | Cryptocurrency tokens | Credit card, PayPal, etc. |
| Ease of Use | Complex for non-tech users | Very user-friendly |
| Cost | Pay-per-use in crypto | Flat monthly subscription |
| Torrenting Safety | Possible but inconsistent | Reliable with P2P servers |
| Government Resistance | High (no central entity) | Vulnerable to legal orders |
| Crypto Wallet Required | Usually yes | No |
| Free Tier | Limited (Orchid has free entry points) | Rare and restricted |
As you can see from this comparison, neither option is universally superior. Additionally, your choice should depend heavily on your use case — which we cover in detail below.
4. Tor vs Decentralized VPN: What’s the Difference?
Tor is often mentioned alongside dVPNs as an alternative to traditional VPNs, and while both use distributed node networks, they are fundamentally different tools.
The tor routes your traffic through three layers of encrypted relays — entry, middle, and exit nodes — making it extremely difficult to trace. However, Tor is notoriously slow, frequently blocked by websites, and not suitable for high-bandwidth activities like streaming or torrenting. A decentralized VPN, by contrast, typically routes through one or two nodes, prioritizing speed and usability while still removing central authority.
“Tor prioritizes anonymity above all else, and dVPNs deliver privacy-preserving internet access at usable speeds—highlighting the core philosophical difference between the two technologies.”
Moreover, Tor is completely free and volunteer-run, while most dVPNs use a token economy. For journalists or activists who need maximum anonymity and can tolerate slow speeds, Tor remains a strong choice. Everyday secure browsing and decentralized VPN censorship bypass, a dVPN is typically the more practical option. For more on Tor’s architecture, the Tor Project’s official documentation is the gold standard.
5. Best Decentralized VPNs for Privacy in 2025
If you’re looking for the best dVPN for privacy in 2025, here are the top options available to US users:
Mysterium Network
Mysterium Network is widely regarded as the most mature and privacy-focused dVPN on the market. Understanding Mysterium Network how it works is straightforward: nodes earn MYST tokens for sharing bandwidth, while users pay micro-amounts per session. Crucially, Mysterium has a verified decentralized VPN no-logs policy enforced at the protocol level — node operators cannot read your traffic. You can also buy a Mysterium node as a dedicated hardware device for passive income. For an in-depth Mysterium Network review, the official Mysterium documentation covers node setup and privacy guarantees in full detail.
Orchid VPN
The Orchid VPN review landscape is generally positive for users who want flexibility. Moreover, Orchid uses a multi-hop architecture and lets users stack bandwidth providers, including some traditional VPN providers, within its network. As a result, users can enjoy enhanced privacy and customizable connection options You fund an Orchid account with OXT tokens, and payment happens automatically per-packet. Orchid is notably accessible for those wondering about dVPN without a crypto wallet — its nanopayment system abstracts much of the complexity.
Sentinel Network
Sentinel is a newer but rapidly growing blockchain VPN built on the Cosmos ecosystem. It supports multiple dVPN apps and has an active developer community pushing for Web3 VPN explained simplicity. It’s particularly popular for decentralized VPN censorship bypass in regions with heavy internet restrictions.
Deeper Network
Deeper Network merges hardware and software, offering a physical device that serves as both a dVPN client and node. It’s one of the more approachable options for non-technical users and supports a decentralized VPN free tier for basic browsing.
6. Mysterium vs NordVPN: Which Should You Choose?
The Mysterium vs NordVPN comparison is ultimately about your priorities. NordVPN is one of the most popular traditional VPNs in the US, with a proven track record, excellent speeds, and a user-friendly app. It has passed independent audits confirming its no-logs policy. Nevertheless, it remains a centralized company subject to court orders.
Choose Mysterium If…
- You don’t trust any single company with your data
- You need censorship bypass in authoritarian regions
- You’re comfortable with crypto payments
- You want to earn passive income as a node
- You’re a journalist, activist, or researcher
Choose NordVPN If…
- You need fast, consistent speeds for streaming
- You want a simple, one-click app experience
- You’re using it for torrenting on P2P servers
- You prefer paying with a credit card
- You don’t want to manage crypto wallets
For most everyday US users, NordVPN’s combination of speed, ease, and audited privacy is hard to beat. Conversely, for those with serious privacy needs — activists, whistleblowers, journalists — the structural guarantees of Mysterium or similar dVPNs are worth the added complexity. For an independent comparison of VPN security standards, PCMag’s VPN analysis is an excellent high-authority reference.
7. Who Should Use a Decentralized VPN?
dVPNs are not for everyone — but for specific groups, they represent the best available privacy tool. Here’s who benefits most:
Journalists and Activists
A decentralized VPN for journalists and activists is particularly valuable because it eliminates the risk of a VPN provider being compelled to hand over user data. With no central authority and no logs to subpoena, dVPNs provide a structural layer of protection that policy-based promises cannot match.
Users in Censored Regions
Because dVPN nodes spread across thousands of residential IPs, they make it significantly harder for governments to block access than traditional VPN server IPs.
As a result, decentralized VPN censorship bypass works effectively. Moreover, censors cannot simply blocklist a known data center; instead, they would have to block millions of ordinary residential addresses. Consequently, users enjoy more reliable and resilient access to the internet.
Privacy-First Tech Users
If you already engage with Web3, hold cryptocurrency, and want to decentralize your entire digital stack, a dVPN fits naturally alongside tools like Brave Browser and encrypted messaging apps.
A Note on Torrenting: Many users ask: is a decentralized VPN safe for torrenting? The answer is: it depends. Some dVPN node operators may not allow BitTorrent traffic. Additionally, speeds can be inconsistent. For heavy torrenting, a traditional VPN with dedicated P2P servers is still more reliable. Learn more about safe online practices at the Jazz Cyber Shield blog.
8. How to Earn Money With a dVPN Node
One of the most unique aspects of the dVPN ecosystem is that you can earn money with a dVPN node by sharing your unused bandwidth. Here’s how it works in practice:
By running a Mysterium node—either on a spare computer or a dedicated Mysterium hardware device—you earn MYST tokens whenever another user routes traffic through your connection. Additionally, your location, uptime, and bandwidth quality directly determine your earnings. Consequently, users in the US consistently report earning meaningful passive income from highly valued residential IPs. Furthermore, this setup allows participants to contribute to a more decentralized and privacy-focused internet ecosystem.
Similarly, Sentinel and Deeper Network nodes earn their respective tokens. The dVPN token incentive model rewards honest nodes and uses token market prices to determine real-world earnings. As Web3 adoption grows, it will increase demand for high-quality dVPN bandwidth through 2025 and beyond.
Getting Started: To buy a Mysterium node or set up software-based node operation, visit the JazzCyberShield resource hub for step-by-step US-based guidance.
9. Limitations and Risks of dVPNs
Despite their significant advantages, dVPNs come with real limitations that every US user should understand before switching.
Speed: Is a Decentralized VPN Slower Than a Regular VPN?
The short answer: yes, typically. A decentralized VPN slower than a regular VPN situation is common because traffic routes through residential nodes with variable connection quality, rather than enterprise-grade data center servers. Speed depends heavily on which node you connect to, their geographic distance, and their current load. Streaming 4K content or gaming with low latency is generally not recommended on most dVPN networks today.
Crypto Wallet Requirement
Most dVPNs still require you to manage a crypto wallet and purchase tokens to pay for bandwidth. While projects like Orchid have simplified this significantly, dVPN without crypto wallet usage is not yet seamless across the board. This remains the biggest barrier to mainstream US adoption.
Can You Trust a Decentralized VPN?
A common concern: can you trust a decentralized VPN? The architectural trust model is stronger than centralized VPNs — but node operators are still routing your traffic. While they cannot decrypt it (encryption prevents this), they can see that traffic is passing through their machine. Using a reputable dVPN with multi-hop routing, like Orchid, adds an additional layer. Additionally, for purely sensitive activities, combining a dVPN with Tor provides the strongest available protection.
Does a Decentralized VPN Hide Your IP Address?
Yes — does a decentralized VPN hide IP address? Absolutely. Your real IP is replaced with that of the exit node, just like a traditional VPN. The difference is that the node operator is a fellow user, not a corporation, making data aggregation at scale significantly harder.
For the latest independent security analysis of dVPN protocols, WIRED’s cybersecurity coverage consistently provides some of the most thorough journalism on privacy tools available.
decentralized VPNdVPNblockchain VPNWeb3 VPNMysteriumOrchid VPNpeer-to-peer VPNdVPN privacycensorship bypassVPN 2025
Frequently Asked Questions
What is a decentralized VPN and how is it different from a regular VPN?
A decentralized VPN (dVPN) routes your internet traffic through a network of peer-operated nodes rather than company-owned servers. A decentralized VPN removes centralized control, avoids storing activity in a central database, and prevents any single entity from being forced to produce user logs. The result is a decentralized VPN no-logs policy that’s structural, not just a corporate promise. For a deeper dive into how this affects your privacy, visit the Jazz Cyber Shield blog.
Is a decentralized VPN safe for torrenting?
It depends on the specific dVPN and node you use. Some node operators restrict BitTorrent traffic. Furthermore, speeds on dVPN networks are generally less consistent than on traditional VPNs with dedicated P2P servers. Therefore, if torrenting is your primary use case, a reputable traditional VPN with P2P support may be more reliable. However, if privacy is your overriding concern, a dVPN still offers stronger structural protection. Consequently, even though performance can be variable, many users prioritize the enhanced security and decentralization it provides
Can I use a decentralized VPN without a crypto wallet?
Most dVPN networks currently require some form of cryptocurrency to pay for bandwidth — this is how the dVPN token incentive model works. However, projects like Orchid have simplified the onboarding process significantly, and some networks like Deeper Network offer limited free tiers. As the ecosystem matures, more dVPN without crypto wallet options are likely to emerge. For now, basic crypto familiarity is recommended for most dVPN platforms.
How does the Mysterium Network work?
Mysterium Network how it works: users connect to the Mysterium app and select an exit node from thousands of community-operated nodes worldwide. Traffic is encrypted and routed through the selected node. Node operators earn MYST tokens for each session they support. The entire payment and verification system runs on a blockchain, eliminating the need for a central corporate entity. You can run a node on a spare computer, a Raspberry Pi, or purchase dedicated Mysterium hardware. Learn more at Jazz Cyber Shield.
Is a decentralized VPN slower than a regular VPN?
Generally, yes. A decentralized VPN slower than a regular VPN comparison is accurate for most current dVPN implementations. Because your traffic routes through residential nodes rather than enterprise data centers, speeds are more variable and often lower. However, the gap is narrowing as dVPN networks grow larger and more nodes become available. For activities requiring consistent high speeds — 4K streaming, gaming, large file transfers — traditional VPNs still have a clear advantage. For privacy-first browsing and secure communications, a dVPN’s speed trade-off is usually acceptable.
Final Verdict: Should You Switch to a dVPN?
The rise of decentralized VPN technology represents a genuine shift in how privacy tools can be built and trusted. For most everyday US internet users who want reliable speed, streaming compatibility, and simple monthly billing, a well-audited traditional VPN like NordVPN remains the practical choice. However, for journalists, activists, privacy researchers, and anyone who cannot afford to trust a single corporate entity with their traffic data, a dVPN offers structural privacy guarantees that no policy document can match.
For serious privacy in 2025, use a layered approach: rely on a trusted traditional VPN for daily use, and choose a blockchain VPN like Mysterium or Orchid for your most sensitive communications. The Web3 VPN ecosystem is maturing rapidly, and within the next few years, user experience improvements will likely make dVPNs accessible to a much wider audience.