Every few months, someone’s ISP sells their browsing data, a government issues a new surveillance order, or a VPN provider gets a court subpoena — and suddenly everyone starts Googling “how to be anonymous online.” If you’re reading this right now, you probably want a straight answer: should you use Tor or a VPN in 2026?
Here’s the honest reality. Neither tool is a magic cloak. Both protect you in different situations, and both fail in ways most people don’t expect. This guide cuts through the noise and gives you exactly what you need to make the right call.
Table of Contents
1. What Is a VPN and How Does It Work?
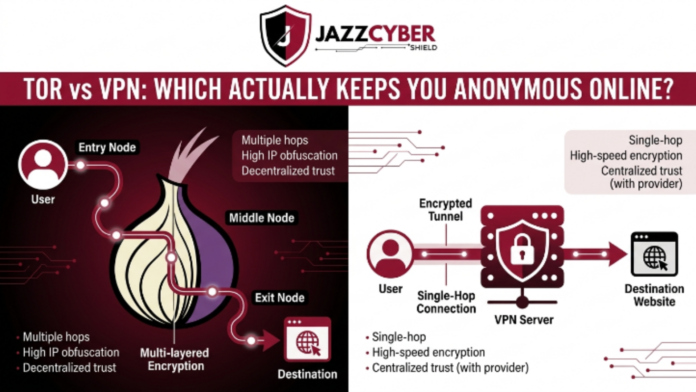
A VPN, or Virtual Private Network, creates an encrypted tunnel between your device and a server run by the VPN provider. When you connect, your internet traffic first goes to that server, then out to the wider internet. As a result, websites and services see the VPN server’s IP address — not yours.
In practice, your ISP in the UK or US can no longer see which websites you visit. Furthermore, anyone snooping on your local Wi-Fi connection sees only scrambled data. This makes VPNs especially useful when you’re on public Wi-Fi in a coffee shop or hotel.
However, the VPN provider itself can still see everything you do. This is the catch that most people miss. You’re essentially moving trust from your ISP to the VPN company. If the VPN company keeps logs, gets hacked, or receives a court order from a US or UK court, your data is on the table.
Reputable VPN providers like ExpressVPN and Mullvad have no-log policies audited by third parties. But “no-log” is a marketing claim until proven in court — and some have failed that test. Therefore, it’s worth knowing what you’re actually trusting.
💡 Quick Fact
VPNs use protocols like OpenVPN, WireGuard, and IKEv2 to encrypt your connection. WireGuard is the fastest and most modern option in 2026, and most leading VPNs support it by default.
2. What Is Tor and How Does It Work?
Tor stands for “The Onion Router.” It routes your traffic through at least three volunteer-operated servers called nodes or relays — an entry node, a middle node, and an exit node. Each relay only knows the node before it and the node after it. Consequently, no single relay knows both who you are and what you’re accessing.
The Tor Project — a US-based nonprofit — develops and maintains this network. It’s the same network journalists, whistleblowers, and activists use to communicate safely. Beyond that, Tor also gives you access to .onion sites, which are websites that exist only within the Tor network and don’t have a public IP address.
The key advantage of Tor over a VPN is that no single entity controls the whole path. Even the Tor Project itself cannot deanonymize you by handing over a log file because there isn’t one. However, Tor has real weaknesses — which we’ll get into shortly.
⚠️ Important Note
Tor encrypts traffic between relays, but the exit node can see your unencrypted traffic if the destination site doesn’t use HTTPS. Always check for the padlock in your browser when using Tor.
3. Tor vs VPN: Key Differences at a Glance
| Feature | VPN | Tor |
|---|---|---|
| Who controls the network? | Single VPN company | Thousands of volunteers globally |
| Speed | Fast (near-normal) | Slow (3+ hops add latency) |
| Anonymity level | Medium (trust VPN provider) | High (decentralized, no single log) |
| IP masking | Yes — shows VPN server IP | Yes — shows exit node IP |
| Encryption | Strong (AES-256 or ChaCha20) | Layered (3 layers of encryption) |
| Cost | $3–$15/month typically | Free |
| Ease of use | Very easy (one-click apps) | Moderate (Tor Browser required) |
| Access to .onion sites | No | Yes |
| Works for streaming | Yes (Netflix, BBC iPlayer, etc.) | No (too slow, gets blocked) |
| Legal in US & UK | Yes | Yes (with caveats) |
4. How Anonymous Is a VPN — Really?
Let’s be direct: a VPN gives you privacy, not anonymity. These are different things. Privacy means others can’t easily see what you’re doing. Anonymity means they can’t link what you’re doing back to you at all. A VPN delivers the first but often falls short of the second.
Here’s why. First, you pay for most VPNs with a credit card or PayPal — both of which tie back to your identity. Moreover, if you create an account with your real email, the VPN company already knows who you are. Even if they don’t log traffic, they might log account activity, payment records, or connection timestamps.
Second, law enforcement in the US and UK regularly issues subpoenas to VPN companies. Some VPNs, despite their no-log claims, have complied and handed over data. This doesn’t mean VPNs are useless — it means you need to choose carefully. Providers like Mullvad accept cash and cryptocurrency payments and don’t require an email to sign up, which reduces this risk significantly.
For everyday privacy — protecting yourself from ISP snooping, advertisers, and data brokers — a good VPN works well. Additionally, for accessing geo-restricted content like BBC iPlayer in the UK or US-only streaming libraries, VPNs are the right tool. But if you need true anonymity because your safety depends on it, a VPN alone is probably not enough.
If you want to understand how VPNs fit into a broader security strategy, check out our guide on Next-Generation Firewalls for 2026 — because your network perimeter matters just as much as your endpoint tools.
5. How Anonymous Is Tor — Really?
Tor is considerably stronger for anonymity than a VPN, but it’s still not bulletproof. The FBI and NSA have successfully deanonymized Tor users before — primarily through browser exploits, JavaScript attacks, and traffic correlation attacks at the network level. So Tor’s strength depends heavily on how you use it.
The biggest mistakes people make with Tor include: logging into personal accounts like Gmail or Facebook while using Tor, downloading files that then call home over your regular connection, and running JavaScript-heavy sites that can fingerprint your browser. In fact, the Tor Browser ships with JavaScript restrictions and privacy settings preconfigured precisely to reduce these risks.
Additionally, exit node attacks remain a real concern. Anyone can run a Tor exit node — including intelligence agencies. If you visit an HTTP site (not HTTPS), the exit node sees your traffic in plain text. That said, in 2026, the vast majority of the web runs on HTTPS, which significantly reduces this risk compared to five years ago.
Tor also has a timing correlation weakness. If a powerful adversary — like a government agency — controls enough of the network and can observe both the entry and exit points of your traffic, they can statistically link the two even without breaking encryption. For most people, this threat isn’t realistic. For journalists, dissidents, or whistleblowers dealing with state-level adversaries, it absolutely is.
🔍 Real-World Context
The US Freedom of the Press Foundation actively recommends Tor for journalists communicating with sources. Similarly, UK-based organizations like Privacy International advocate Tor use for at-risk individuals. These aren’t fringe use cases — they’re mainstream privacy tools used by professionals.
6. Speed and Performance: Which One Wins?
This isn’t a close contest. VPNs win on speed — by a lot. A decent VPN using the WireGuard protocol typically cuts your speed by 10–20% at most. In contrast, Tor routes your traffic through at least three different countries, and average speeds often drop by 70–90% compared to your baseline connection.
As a result, Tor is practically unusable for video calls, HD streaming, large file downloads, or any latency-sensitive activity. Moreover, many websites — including Cloudflare-protected sites and major platforms — block or add CAPTCHAs to Tor exit nodes because they associate them with spam and abuse. This makes basic web browsing on Tor genuinely frustrating for everyday use.
If you run a small business or work remotely in the US or UK and need a secure connection that doesn’t slow your workflow, a VPN is the only practical choice. Tor works well for specific, privacy-critical tasks — reading sensitive information, accessing .onion resources, or communicating anonymously — but it’s not a daily driver.
7. Which One Should You Use? (By Use Case)
Use a VPN if you want to:
Protect your connection on public Wi-Fi in airports, hotels, or coffee shops across the US or UK. Access geo-restricted content like US Netflix from the UK, or BBC iPlayer while traveling abroad. Furthermore, keep your ISP from selling your browsing data — both the US and UK have weak ISP data protection laws compared to the EU. Work remotely and connect securely to your company’s internal systems. Generally, reduce your digital footprint without sacrificing speed or convenience.
Use Tor if you want to:
Communicate with sources as a journalist and need your identity protected from newsroom server logs. Access .onion sites or resources not available on the public web. Bypass censorship in countries that block VPN services — Tor has bridges specifically designed to work around this. Additionally, protect yourself against ISP-level traffic analysis when you genuinely cannot trust any VPN provider. Research sensitive topics where even a VPN’s logs could implicate you.
Use both (Tor over VPN) if:
You need maximum protection and can tolerate very slow speeds. Your threat model includes adversaries who can observe your internet connection at the ISP level. You’re in a situation where using Tor directly would attract attention — connecting to a VPN first hides the fact that you’re using Tor at all.
🧭 Quick Decision Guide
Everyday privacy from advertisers and ISPs → VPN
Streaming and geo-unblocking → VPN
Whistleblowing or journalist source protection → Tor
Accessing .onion sites → Tor
Maximum anonymity with serious threat model → Tor + VPN combined
8. Can You Use Tor Over VPN?
Yes, and it’s more useful than you might think. When you run Tor over a VPN, you first connect to your VPN, then launch Tor on top of it. This way, your ISP sees only VPN traffic — not Tor traffic. Additionally, the Tor entry node sees your VPN server’s IP rather than your real IP, which adds a layer of protection even if the Tor network is partially compromised.
The downside, however, is obvious: you stack the speed penalties of both tools. Your connection will be slow. Furthermore, you still have to trust the VPN for that outer layer, so choosing a privacy-focused VPN that accepts anonymous payments becomes even more important in this setup.
There’s also the reverse: VPN over Tor, where you connect to Tor first and then to a VPN. This is technically complex and rarely recommended because it adds little benefit for most users while creating new attack surfaces. Therefore, if you go the combined route, Tor over VPN is the standard approach.
For organizations managing network security across multiple endpoints, combining these tools with a solid perimeter strategy is essential. The team at Jazz Cyber Shield covers layered security solutions that pair well with endpoint privacy tools like VPNs and Tor.
9. Is Tor or VPN Legal in the US and UK?
In both the United States and the United Kingdom, using a VPN or Tor is completely legal. There is no law that prohibits either tool for law-abiding citizens. However, the legal question that actually matters is: what you do while using them.
In the US, the Electronic Frontier Foundation (EFF) consistently defends the right to use privacy tools. The Fourth Amendment protects against unreasonable searches, and VPNs and Tor are legal methods of protecting your data. That said, US law enforcement — particularly the FBI — actively monitors Tor and has taken down numerous illegal marketplaces on the dark web. The tool is legal; illegal activity on it is not.
In the UK, the Investigatory Powers Act 2016 gives authorities broad surveillance powers, including the ability to compel companies to hand over data. However, using Tor or a VPN is not illegal under this act. The UK’s National Cyber Security Centre (NCSC) actually recommends VPN use for businesses to protect their networks. Moreover, journalists and privacy advocates use both tools freely.
The bottom line: if you’re using Tor or a VPN to protect your privacy, stream content, or work securely, you’re on solid legal ground in both countries. Problems arise only when these tools facilitate illegal activity — and in that case, the law catches up more often than people expect.
⚠️ Note for UK Users Some UK internet providers briefly considered blocking Tor exit nodes under pressure, but this has not been implemented as policy. Tor remains accessible and legal in the UK as of 2026.
10. Final Verdict: Tor vs VPN in 2026
Here’s the thing — asking “which is better” is the wrong question. They solve different problems, and the one you need depends entirely on your actual situation.
If you’re an everyday internet user in the US or UK who wants to stop your ISP from selling your browsing history, protect yourself on public Wi-Fi, and maybe unblock streaming content while traveling — get a reputable VPN. Pick one with a verified no-log policy, WireGuard support, and ideally anonymous payment options. It will be fast, easy to use, and handle 95% of privacy needs.
If you’re a journalist, researcher, activist, or anyone who genuinely needs their identity protected from adversaries with real resources — use Tor. Accept the speed trade-off, learn how to use it correctly, and avoid the common mistakes that undo its protections. Additionally, consider Tor over VPN if your ISP-level visibility is a concern.
For most people reading this in 2026, the honest answer is: start with a good VPN, learn how it protects you and where it doesn’t, and add Tor selectively for situations where you need stronger anonymity. As cybersecurity threats evolve, understanding both tools gives you real options rather than false confidence in either one alone.
Want to go deeper on network-level security? Read our breakdown of Next-Generation Firewalls in 2026 — because your privacy tools work best when your broader network is locked down too. And if you’re looking for security hardware and solutions for your home or business, explore what Jazz Cyber Shield offers.
Frequently Asked Questions — Tor vs VPN (2026)
Q1Is Tor better than a VPN for privacy in 2026?
It depends on what you mean by “better.” Tor offers stronger anonymity because no single server holds your full traffic path — your data bounces through three volunteer-run relays, and no one relay knows both who you are and what you’re accessing. However, a VPN is far faster, easier to use, and protects you reliably from everyday threats like ISP tracking, ad surveillance, and unsecured Wi-Fi. For most people in the US and UK who want day-to-day privacy, a no-log VPN is the more practical choice. For journalists, whistleblowers, or anyone facing a serious adversary, Tor — or Tor combined with a VPN — is the stronger option. Neither tool is universally “better”; they protect against different threats.
Q2Can the government see what you do on Tor or a VPN?
With a VPN, government agencies in the US and UK can subpoena the VPN provider for your data. If the provider keeps logs, those logs get handed over. This is why no-log VPNs that have passed independent audits — like Mullvad or ProtonVPN — matter so much. With Tor, the situation is different. There are no central logs to subpoena because no single server knows the full picture. However, agencies like the NSA and GCHQ have capabilities for large-scale traffic analysis, meaning they can sometimes correlate Tor entry and exit traffic to identify users — especially with long sessions. In practice, state-level surveillance of Tor requires significant resources and is not routine. For ordinary users, both tools provide meaningful protection against government surveillance, as long as you don’t make operational security mistakes like logging into personal accounts while using them.
Q3Does using Tor or a VPN slow down your internet speed?
Yes, both reduce your speed — but to very different degrees. A quality VPN using WireGuard typically cuts your connection speed by 10–20%, which most users barely notice during browsing, streaming, or video calls. Tor, on the other hand, routes your traffic through at least three relays spread across different countries, which often reduces speed by 70–90% compared to your baseline. As a result, Tor is impractical for HD video streaming, large downloads, or real-time communication. Furthermore, many popular websites add CAPTCHAs or block Tor exit nodes entirely, which makes even basic browsing noticeably slower. If speed matters to you — and for most people it does — a VPN is the only realistic daily tool. Use Tor for specific tasks where anonymity outweighs the inconvenience of slower speeds.
Q4 What happens if a VPN provider gets hacked or receives a court order?
This is the question every VPN user should ask. If a VPN provider gets hacked, any data they store — including connection logs, account details, and payment records — can be exposed. If they receive a court order in the US or UK, they are legally required to hand over whatever data they hold. This is precisely why the “no-log” policy matters so much. A VPN that genuinely stores no traffic logs has nothing to hand over, even under legal compulsion. Mullvad has demonstrated this in practice — when Dutch police seized their servers in 2023, investigators found nothing because there was nothing stored. Additionally, VPNs based in countries outside the Five Eyes intelligence alliance (US, UK, Canada, Australia, New Zealand) face fewer legal obligations to cooperate with foreign surveillance requests. Therefore, when choosing a VPN, verify their no-log claims through independent audits rather than relying on marketing alone.
Q5 Should I use Tor and a VPN together, and how do I set it up?
Using Tor over a VPN — meaning you connect to your VPN first, then launch the Tor Browser — is a legitimate approach for users who need extra protection. The main benefit is that your ISP sees only encrypted VPN traffic, not Tor traffic. This is useful in the UK and US because some ISPs flag or throttle Tor connections. Moreover, the Tor entry node sees your VPN server’s IP instead of your real IP, which adds a layer of separation. To set it up: connect to your VPN as normal, then open the Tor Browser. That’s it — no special configuration needed. However, be aware that the combined setup stacks both speed penalties, making it noticeably slow. This setup works well for high-risk situations, but for everyday use, either tool alone is sufficient.