Zero trust network security has officially become the most urgent cybersecurity shift of 2026 — and if your organization is still running on a traditional VPN, you are already behind. According to Zscaler’s ThreatLabz 2026 VPN Risk Report, 81% of organizations plan to implement zero trust strategies within the next 12 months, and 65% are actively replacing VPN services this year alone.
That number is not a coincidence. In 2025, 56% of organizations reported a breach directly exploited through VPN vulnerabilities. At the same time, the global Zero Trust Security market is projected to surge from $36.5 billion in 2024 to $78.7 billion by 2029 — growing at a 16.6% CAGR. If your IT infrastructure still relies on “trust everyone inside the network,” you are operating on a model that attackers have already cracked.
This guide explains exactly what zero trust network security is, why traditional perimeter defenses are failing in 2026, and how your organization can implement ZTNA step by step — including the hardware you need to do it right.
Table of Contents
What Is Zero Trust Network Security?
Zero trust network security is a cybersecurity framework built on one non-negotiable principle: never trust, always verify.
Unlike traditional perimeter-based security — where every device and user inside the corporate network is automatically trusted — zero trust treats every access request as a potential threat, regardless of where it originates. Whether a request comes from an employee in the office, a remote contractor, or an internal server, zero trust demands continuous verification before granting access.
The concept was first formalized by Forrester Research analyst John Kindervag in 2010. However, it wasn’t until 2020–2026 — driven by the explosion of remote work, cloud migration, and AI-powered attacks — that zero trust stopped being a theory and became a business necessity.
At its core, zero trust network security relies on three foundational pillars:
1. Verify Every Identity Explicitly Every user, device, and application must prove its identity at every access point. This means multi-factor authentication (MFA), risk-based scoring, and continuous behavioral monitoring — not just a one-time login.
2. Use Least-Privilege Access Users and systems receive only the minimum access they need to perform their specific function. No blanket permissions. No broad network access. If an attacker does compromise a user account, the blast radius stays contained.
3. Assume Breach Zero trust operates under the assumption that a breach has already occurred or is occurring. This mindset drives micro-segmentation, end-to-end encryption, and real-time anomaly detection — making lateral movement across the network significantly harder.
Why Traditional VPNs Are Failing in 2026
For nearly 30 years, VPNs were the gold standard for secure remote access. Today, they have become one of the biggest liabilities on the network. Here is why IT teams across the USA are moving away from them fast.
VPNs grant broad network access. When a user connects via VPN, they gain access to large portions of the corporate network — not just the specific application they need. If that user’s credentials are stolen, attackers inherit the same broad access. This is exactly how Akira ransomware tore through SonicWall-connected networks in 2025 and 2026. We covered that attack vector in detail in our Akira Ransomware SonicWall Attacks: 2026 Survival Guide.
VPNs are internet-facing attack surfaces. Because VPN gateways are publicly accessible, attackers can scan for them, identify vulnerable versions, and exploit unpatched CVEs before your IT team has finished their morning coffee. The Firestarter malware campaign against Cisco firewalls in April 2026 demonstrated exactly how these perimeter devices become high-value targets.
VPNs create performance bottlenecks. Routing all traffic through a central VPN gateway creates latency, especially for cloud-first organizations. Users complain, IT teams scramble, and productivity drops. Zero trust network access (ZTNA) solves this by providing direct, application-specific connections without centralized traffic routing.
AI-powered attacks target VPN vulnerabilities at scale. As we documented in our VPN Security Risks 2026 article, automated AI tools can now scan millions of IP addresses for vulnerable VPN endpoints in hours, compress exploit development timelines from weeks to hours, and launch credential-stuffing attacks using AI-generated password variations at unprecedented speed.
The conclusion is unavoidable: the VPN era is ending. Zero trust network security is the replacement architecture.
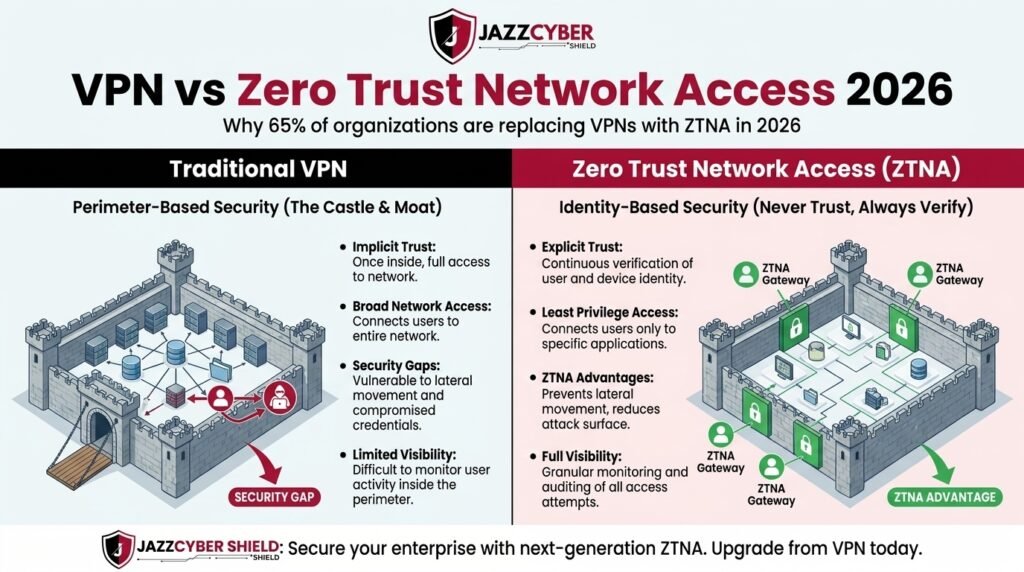
Zero Trust vs. Traditional Perimeter Security: Key Differences
Understanding why zero trust works requires understanding what it replaces. Here is a direct comparison of the two models.
Traditional Perimeter Security (Castle-and-Moat Model) The old model assumes that everything inside the network perimeter is safe. The firewall is the wall. Once you are inside, you are trusted. This works when employees sit at fixed desks in a single building. It fails catastrophically when users work from home, access cloud apps, and bring their own devices.
Zero Trust Network Security The new model assumes there is no perimeter. Users work from everywhere. Applications live in multi-cloud environments. Devices may or may not be corporate-managed. Zero trust responds by moving security controls from the network edge to the identity and application layer, verifying continuously rather than trusting implicitly.
The practical difference is significant. In a traditional perimeter model, one compromised credential gives an attacker lateral movement across the entire network. In a zero trust model, that same compromised credential grants access only to the specific applications and data that user was authorized to access — and even that access is continuously monitored for anomalous behavior.
How Zero Trust Network Access (ZTNA) Actually Works
Zero Trust Network Access (ZTNA) is the technical implementation layer of zero trust principles. It replaces VPN tunnels with application-specific, identity-verified access connections. Here is the step-by-step flow.
Step 1 — User or Device Requests Access An employee tries to access a business application — say, the company ERP system. Instead of connecting to the corporate network first, the request goes to a ZTNA broker or policy engine.
Step 2 — Identity Verification The ZTNA system verifies the user’s identity through MFA, single sign-on (SSO), or certificate-based authentication. It also checks device health — is the device managed? Is it running current patches? Does it meet security posture requirements?
Step 3 — Contextual Risk Scoring The system scores the access request against contextual signals: What time is it? Where is the user located? Is this a typical access pattern for this user? Has this device been seen before? AI-powered behavioral analytics flag anomalies in real time.
Step 4 — Least-Privilege Access Granted If the identity and context checks pass, the user receives access to the specific application — and only that application. They cannot browse the broader network. They cannot hop laterally to other systems.
Step 5 — Continuous Monitoring Even after access is granted, the session is monitored continuously. If behavior changes — unusual data download volumes, access to previously untouched directories, login from an unexpected geographic location — the session is flagged or terminated automatically.
This is what makes zero trust so powerful: it transforms security from a gate you pass once to a continuous verification loop that never stops.
The Hardware Behind a Zero Trust Architecture
Implementing zero trust network security is not purely a software exercise. The right hardware plays a critical role — particularly next-generation firewalls (NGFWs) with built-in ZTNA capabilities, network switches with micro-segmentation support, and access points with identity-aware policy enforcement.
Next-Generation Firewalls for ZTNA
Modern NGFWs from vendors like Fortinet, Cisco, SonicWall, and WatchGuard are purpose-built to enforce zero trust policies at the network edge and across distributed environments.
Fortinet FortiGate implements zero trust via the FortiOS Security Fabric, which integrates identity-based access control, SSL inspection, and application-level policy enforcement. The FortiGate 60F — starting from $450 — is the best-seller for mid-size businesses implementing zero trust, delivering AI-powered threat protection at 10 Gbps throughput. You can explore the full Fortinet firewall range on Jazz Cyber Shield.
Cisco’s approach to ZTNA runs through the Cisco Secure Access framework, combining Duo MFA, Cisco Identity Services Engine (ISE), and Cisco Umbrella for DNS-layer security. The Cisco Catalyst switch series supports granular VLAN segmentation that is foundational to any micro-segmentation strategy.
SonicWall TZ270 — available from $350 — delivers real-time Deep Packet Inspection (DPI) and cloud-managed threat intelligence, both essential capabilities for enforcing zero trust policies at branch office locations. Browse the full SonicWall firewall lineup here.
WatchGuard Firebox offers a complete UTM security suite with multi-WAN support that is particularly effective in zero trust deployments where traffic must be inspected across multiple uplinks without performance degradation.
Network Switches for Micro-Segmentation
Micro-segmentation is one of zero trust’s most powerful weapons — it divides the network into small, isolated zones so that even if an attacker breaches one segment, they cannot reach others. This requires managed switches capable of enforcing policy at the access layer.
HPE Aruba switches — particularly the CX 6300 Series with AOS-CX OS and REST API automation — are specifically designed for zero trust network architectures, enabling dynamic policy enforcement at the edge. Similarly, Cisco Catalyst 9200 and 9300 series switches provide the Layer 2/3 segmentation required for enterprise-grade ZTNA deployments.
Access Points with Identity-Aware Policies
In a zero trust environment, wireless access cannot operate on a flat, trusted-by-default SSID structure. Access points must enforce device posture checks and identity-based policies at the point of association.
HPE Aruba AP-515 WiFi 6 access points include built-in IoT support and AI-powered WLAN optimization — making them ideal for zero trust wireless deployments where devices of varying trust levels must be isolated from each other dynamically.
Step-by-Step: How to Implement Zero Trust in Your Organization
Transitioning to zero trust network security does not happen overnight. However, following a structured, phased approach makes it manageable — even for small and mid-size businesses. Here is a practical six-step framework.
Step 1 — Identify and Classify Your Protect Surface Rather than trying to secure everything at once, zero trust starts by identifying your most critical data, applications, assets, and services (DAAS). Map what you must protect first. This is your protect surface.
Step 2 — Map Transaction Flows Understand how sensitive data moves across your network. Which applications access which databases? Which users need access to which systems? This mapping reveals your current trust dependencies and the gaps you need to close.
Step 3 — Architect Your ZTNA Environment Design your micro-segmentation zones, define your identity and access management (IAM) policies, and choose your ZTNA broker or gateway. For most SMBs, this is built around the next-generation firewall at the core.
Step 4 — Deploy MFA and Identity Controls Multi-factor authentication is non-negotiable in a zero trust architecture. Deploy MFA across all users, all applications, and all admin accounts immediately. Add device health checks and risk-based authentication policies.
Step 5 — Enforce Least-Privilege Access Review every user account and application permission in your environment. Remove excessive permissions. Implement role-based access control (RBAC). Apply just-in-time (JIT) access for privileged accounts.
Step 6 — Monitor, Detect, and Respond Continuously Zero trust is not a set-it-and-forget-it configuration. Deploy SIEM, behavioral analytics, and endpoint detection to monitor every session in real time. Set up automated responses to anomalous activity. Review your trust policies quarterly.
Zero Trust Compliance: What Regulations Require in 2026
Zero trust is no longer purely a best practice — it is increasingly a regulatory requirement. Organizations operating in the USA need to be aware of the following compliance mandates that explicitly align with zero trust principles.
The NIST SP 800-207 Zero Trust Architecture standard provides the federal baseline for ZTNA implementation and is referenced by FedRAMP, CMMC 2.0, and multiple state-level cybersecurity frameworks. The EU Cyber Resilience Act (CRA), which begins mandatory vulnerability reporting in September 2026, pushes security-by-design requirements that directly complement zero trust architecture. HIPAA, PCI-DSS v4.0, and CCPA/CPRA all include provisions for least-privilege access, network segmentation, and continuous monitoring that map directly onto zero trust implementation frameworks.
For SMBs and enterprises alike, aligning with zero trust principles is simultaneously the right security decision and the right compliance decision.
Common Zero Trust Implementation Mistakes to Avoid
Many organizations begin their zero trust journey with the right intentions but stumble on predictable mistakes. Here are the most common ones — and how to avoid them.
Treating zero trust as a product purchase, not an architecture. No single vendor delivers “zero trust in a box.” Zero trust is an architectural philosophy implemented through multiple integrated tools and policies. Buying a ZTNA product without redesigning your access policies achieves almost nothing.
Neglecting non-human identities. In 2026, Gartner identifies securing machine identities — AI agents, service accounts, API keys, and automation scripts — as one of the top CISO priorities. Zero trust must extend to these non-human actors, not just employees.
Skipping micro-segmentation. Many teams implement strong identity verification at the edge but leave their internal network flat. Without micro-segmentation, a compromised endpoint can still move laterally through the network. Managed switches with policy-level segmentation are essential.
Moving too fast without user training. Zero trust implementations that create friction for legitimate users generate shadow IT — employees find workarounds that undermine the entire security model. Change management and user education must run in parallel with technical deployment.
The Bottom Line: Zero Trust Is Not Optional in 2026
The data is decisive. Enterprises are pivoting away from legacy VPN systems that fail to meet the remote access demands of businesses today, with 81% actively implementing zero trust frameworks. The global Zero Trust Security market is projected to grow from USD 36.5 billion in 2024 to USD 78.7 billion by 2029, driven by rising cyber threats, cloud migration, and stricter data protection regulations. CIOReportsnreports
Zero trust network security is no longer a future-state ambition reserved for Fortune 500 enterprises. It is the practical, deployable answer to the credential-based attacks, ransomware campaigns, and AI-powered threats that are targeting SMBs and mid-market organizations with increasing frequency in 2026.
The good news is that the hardware and software ecosystem for ZTNA implementation has never been more mature or more accessible. Whether you are deploying a Fortinet FortiGate for AI-powered policy enforcement, Cisco Catalyst switches for micro-segmentation, or SonicWall TZ Series appliances for DPI at the branch level, the tools exist to build a production-grade zero trust architecture at a budget that makes sense for your business.
If you are ready to move beyond VPNs and implement zero trust for your organization, explore our full range of enterprise firewalls, managed switches, and access points — all genuine, authorized hardware from the world’s leading vendors, shipped fast from St. Petersburg, Florida.
Frequently Asked Questions About Zero Trust Network Security
What is the difference between zero trust and a traditional firewall? A traditional firewall secures the network perimeter — it decides what traffic enters and exits the network boundary. Zero trust goes further by continuously verifying every access request inside and outside the network, enforcing least-privilege access at the identity and application layer, not just the edge.
Can small businesses implement zero trust? Yes. Zero trust is scalable. SMBs can start with MFA deployment, NGFW with application-level policy enforcement, and VLAN-based micro-segmentation — all achievable with hardware starting under $500. The key is phased implementation, not attempting to transform everything at once.
Is zero trust the same as ZTNA? Zero trust is the overall security philosophy. ZTNA (Zero Trust Network Access) is the specific technology that implements zero trust principles for network and application access — replacing VPN tunnels with identity-verified, application-specific connections.
How long does a zero trust implementation take? For most SMBs, a basic zero trust architecture — covering MFA, NGFW policy enforcement, and network segmentation — can be operational within 60 to 90 days. A full enterprise-grade implementation with behavioral analytics and comprehensive micro-segmentation typically takes 6 to 18 months.
Which firewall brands support zero trust best? Fortinet, Cisco, SonicWall, WatchGuard, and Palo Alto Networks all offer robust zero trust capabilities. For SMBs in the USA, Fortinet and SonicWall provide the best combination of ZTNA features, cost-effectiveness, and ease of management.
Jazz Cyber Shield is a USA-based authorized reseller of Fortinet, Cisco, SonicWall, WatchGuard, HPE Aruba, and other leading enterprise IT security brands. All products ship fast from St. Petersburg, Florida. Browse our full firewall and network security hardware catalog.