You open your VPN app, hit connect, and assume you’re invisible. Your browsing history — private and IP address – hidden. Your identity — protected.
But what if that assumption is dead wrong?
What if the very tool you’re trusting to protect your privacy is secretly building a detailed log of everything you do online — and then handing that data over to government agencies, third parties, or leaving it sitting wide open on an unsecured server?
This isn’t a hypothetical. In fact, this happened. Moreover, it occurred multiple times. Additionally, the evidence came straight from federal court documents, FTC complaints, and cybersecurity researchers who found terabytes of “non-existent” logs floating in the open.
Furthermore, in this article, we expose 5 VPNs that lied about their no-log policies, then reveal exactly what data they collected, and finally explain how real, hardware-backed network security protects you without relying on marketing promises.
What Is a “No-Log Policy” — And Why You Cannot Just Take Their Word For It
A no-log policy — also called a zero-log or logless policy — is a VPN provider’s promise that they do not collect, store, monitor, or share any record of your online activity. That includes your real IP address, websites visited, connection timestamps, bandwidth data, and session information.
On paper, it sounds like the gold standard of digital privacy.
In reality, it is often nothing more than a marketing headline buried beneath a privacy policy full of loopholes — and when law enforcement comes knocking, the truth always surfaces.
At least three different “no-logs” VPNs have been publicly caught logging their users, with released court documents proving the deception while these services continued claiming zero-log status. CyberInsider
If you run a business and need protection that goes beyond trust claims, the answer starts at the hardware level. Explore enterprise-grade Fortinet Firewalls and SonicWall Firewalls — solutions built for organizations where “trust us” is never enough.
🔴 5 VPNs Caught Lying About Their No-Log Policy
1. PureVPN — Handed User Logs Directly to the FBI

What They Claimed: “PureVPN does not keep any records of your activities.”
What Actually Happened: They maintained detailed session logs and provided them to federal investigators on request.
When Ryan Lin was investigated by the FBI for cyberbullying, hacking, and harassment, federal agents approached PureVPN after discovering he had used the service. PureVPN was able to provide logs that revealed the exact IP addresses Lin used to carry out his cyber threats — directly contradicting their public “zero records” promise. All Things Secured
Released court documents proved that PureVPN was logging its users for the FBI, all while openly marketing itself as a zero-log VPN service. CyberInsider
If PureVPN had truly kept no logs, the FBI investigation would have ended there. Instead, PureVPN’s data led directly to a federal conviction.
This is not a gray area. This is a documented, proven lie — and it set the tone for public scrutiny of the entire VPN industry.
What this means for businesses and individuals: Software-layer privacy promises can collapse the moment a government letter arrives. Organizations that handle sensitive client data need infrastructure-level enforcement. A properly configured enterprise firewall enforces traffic rules at the network perimeter — regardless of what any VPN app claims.
2. IPVanish — Government Compliant, Users Left in the Dark

What They Claimed: “IPVanish does not collect or log any traffic or use of its VPN service.”
What Actually Happened: They were secretly logging user activity and cooperated with US federal authorities.
Court documents revealed that IPVanish was logging users at the request of US government officials CyberInsider — a direct contradiction of the no-log policy displayed prominently on their website and marketing materials.
The case involved a child exploitation investigation. While the moral outcome of that specific case is a separate discussion, the technical reality is undeniable: IPVanish was logging user activity in direct violation of their own published privacy policy. Any user — journalist, activist, whistleblower, privacy-conscious professional — who trusted IPVanish based on their no-log promise was misled.
IPVanish has since been sold to new ownership and updated their policies. But the betrayal of user trust is permanently documented in federal court records.
The lesson for network administrators: A VPN subscription is not a security policy. Managed network switches and hardware firewalls give your organization actual control over what traffic flows through your infrastructure — not a promise from a software company subject to government subpoena.
Also worth reading: Why 60% of Small Businesses Close Within 6 Months of a Cyberattack — and understand why layered security matters far more than any single tool.
3. HideMyAss (HMA) VPN — They Logged Your Ass Right Into Prison

What They Claimed: “We do not monitor, record, or store VPN logs.”
What Actually Happened: They handed logs to British and US authorities, and their users went to prison.
HideMyAss VPN was found to be logging users for a US criminal case involving hacking. The HideMyAss users went to jail and learned that HideMyAss will log your ass. CyberInsider
The most famous victim of HMA’s logging was Cody Kretsinger, a member of the LulzSec hacking group. First, British authorities requested connection logs from HMA’s UK parent company. Then, HMA complied. As a result, the logs traced directly back to Kretsinger’s real identity, and he was arrested and convicted in the United States.
HideMyAss has handed customer information over to the police GreyCoder, and this event remains one of the most frequently cited examples of VPN dishonesty in cybersecurity history.
HMA later defended their actions by referencing their terms of service — claiming they never promised to protect users from lawful law enforcement requests. But their public marketing had absolutely claimed exactly that. When a company hides behind fine print after being caught, the “no-log” promise was always hollow.
For businesses: Don’t let a VPN app be the only thing standing between your data and exposure. Check out WatchGuard Firewalls — hardware-enforced network security trusted by enterprises across North America and Europe.
Also explore: Hacked Security Camera Websites: What They Are and How to Stop Them — because your physical and digital perimeters must be protected together.
4. UFO VPN (+ 6 Sister VPNs) — 1.2 Terabytes of “Non-Existent” Logs Found Online
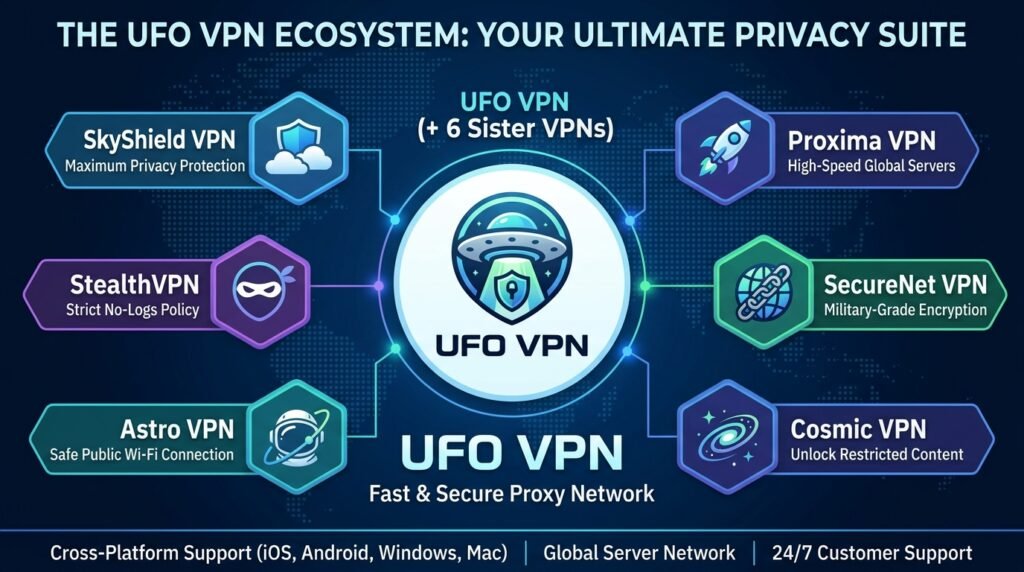
What They Claimed: “UFO VPN keeps no logs. Zero. None.”
What Actually Happened: Over 1.2 terabytes of user logs were discovered sitting on a completely unsecured, publicly accessible server.
This is the most catastrophic mass exposure of fake no-log claims in VPN history. Recently, a team of security researchers discovered an Elasticsearch database left wide open — no password, no encryption, no access control — additionally, it contained detailed logs from seven VPN services that all shared the same server infrastructure.
The exposed cluster contained records of websites visited, as well as connection logs, including people’s names, subscribers’ email and home addresses, along with plain-text passwords, Bitcoin and PayPal payment information, plus messages to support desks, device specifications, and account information. The Register
Each of these VPNs claimed that their services are “no-log” VPNs, meaning they don’t record any user activity on their apps. However, researchers found multiple instances of internet activity logs on their shared server — in addition to personally identifiable information including email addresses, clear-text passwords, IP addresses, home addresses, phone models, device IDs, and other technical details. The Register
The seven VPNs caught in this single exposure: UFO VPN, Fast VPN, Free VPN, Super VPN, Flash VPN, Secure VPN, and Rabbit VPN — all running on the same backend infrastructure, all claiming to keep zero logs, all storing the same mountains of user data.
This was not a government request. VPN was not a court order. This was pure negligence — they were lying about logging everything while simultaneously leaving all that data completely unprotected on the public internet.
The hardware alternative: Cisco Network Switches and HPE Aruba Switches give network administrators real control over data flows — with no third-party software company holding your sensitive data on an unknown server somewhere in the world.
For home network users: What Is a VLAN and Why Every Home Network Needs One in 2026 — network segmentation in plain language, explained by Jazz Cyber Shield.
5. Hotspot Shield — FTC Complaint, Exposed IPs, and Zero Independent Audits
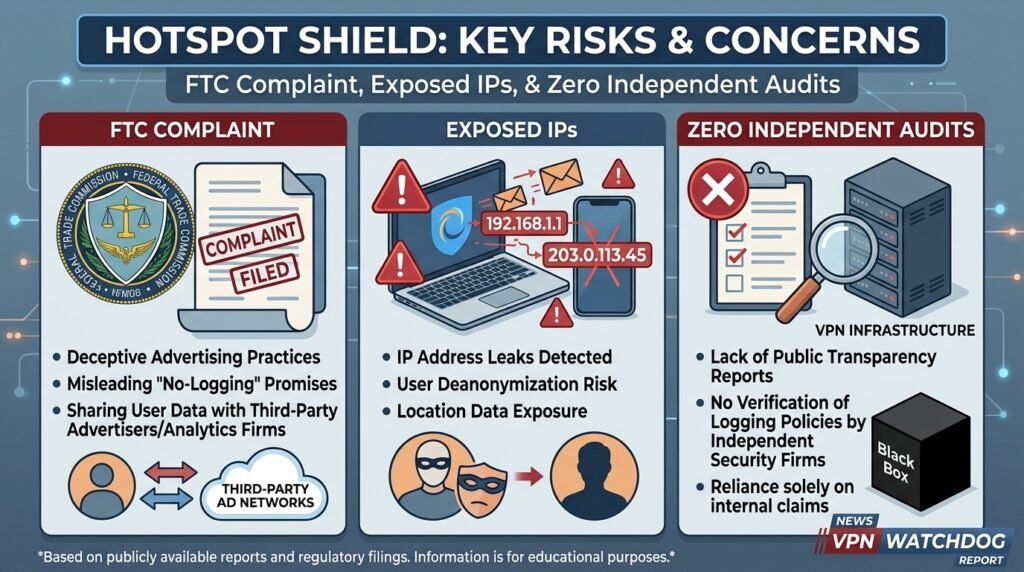
What They Claimed: “Hotspot Shield does not track, log, or share your browsing activities.”
What Actually Happened: A serious security vulnerability exposed real user IP addresses, and a formal FTC complaint alleged unfair and deceptive trade practices.
A vulnerability (CVE-2018-6460) in Hotspot Shield allowed any local program to directly call a web API exposed by the VPN app and reveal users’ real IP addresses as well as Wi-Fi SSIDs, thereby completely exposing users who believed they were protected. Redact
Hotspot Shield’s response was lacking — initial private disclosure went unanswered for weeks, prompting the researcher to take it public. Hotspot Shield issued a patch within 48 hours, but it still operates without an independent no-logs audit, meaning overall transparency remains lacking. Redact
The Center for Democracy & Technology filed a 14-page complaint about Hotspot Shield with the FTC, alleging unfair and deceptive trade practices. GreyCoder
To this day, Hotspot Shield has never submitted to a comprehensive, independent third-party audit of their no-log claims. Consequently, users have no external verification — instead, they must rely solely on the company’s word.
In cybersecurity, “trust us” is not a policy. It is a liability.
For users who want verified protection: Read WPA2 vs WPA3: Is Your Home Wi-Fi Secure? (2026 Guide) — and pair your network with enterprise-grade access points that support WPA3, modern encryption standards, and real-time threat monitoring.
📊 VPN Honesty Scorecard: Caught vs. Verified
| VPN | Claimed | Reality | Verdict |
|---|---|---|---|
| PureVPN | Zero logs | FBI received full IP logs | ❌ LIED |
| IPVanish | No traffic logs | US government received session logs | ❌ LIED |
| HideMyAss | No logs stored | UK/US police received connection logs | ❌ LIED |
| UFO VPN | Zero activity logs | 1.2TB of logs exposed publicly | ❌ LIED |
| Hotspot Shield | No tracking | FTC complaint + live IP leak vulnerability | ❌ DECEPTIVE |
| ExpressVPN | No logs | Turkish server seized — zero user data found | ✅ HELD UP |
| ProtonVPN | No logs | Annual independent audits verified, Swiss jurisdiction | ✅ VERIFIED |
| Mullvad | No logs | Swedish police raid — office emptied with nothing | ✅ PROVEN |
🔒 What Actually Protects You Beyond a VPN?
VPNs are software running on third-party servers you do not control. For example, a subpoena, or a misconfigured database, and even a simple CVE vulnerability can unravel every privacy promise within seconds.
Therefore, real security is built in layers — first, hardware forms the foundation.
Enterprise-Grade Firewalls A Fortinet Firewall or SonicWall enforces traffic policy at the network perimeter — inspecting, filtering, and blocking threats before they reach any device. This is the first line of defense that no VPN app can replicate.
Managed Network Switches Cisco Switches and HPE Aruba Switches give administrators granular control over which devices can communicate, what traffic is permitted, and how data moves across your internal network. Network segmentation stops lateral movement dead.
First, replace consumer-grade routers with enterprise access points that support WPA3 encryption, while enabling VLAN segmentation, and use centralized management, thus creating the backbone of any secure wireless infrastructure.
Physical Security Cameras Your digital security posture is incomplete without physical perimeter control. Axis Security Cameras and Hikvision Cameras deliver enterprise-grade surveillance with encrypted storage and remote management.
More from the Jazz Cyber Shield blog:
- How Hackers Break Into Security Cameras (And How to Protect Yours)
- Is Your Wi-Fi 6 Router Actually Safe? Security Settings You Must Change in 2026
- Hikvision vs Axis Security Cameras: Which Is Safer in 2026?
🕐 Recent Update: The VPN Audit Era — 2025 & 2026
The cybersecurity industry is finally demanding evidence instead of promises. Independent third-party audits are now the benchmark that separates trustworthy VPNs from marketing machines.
Mullvad passed several independent audits in 2025 without any high-severity findings. Additionally, Swedish police raided its office under a German warrant but found no customer data to seize, thereby proving its no-logs claims in practice. Meanwhile, Redseclabs confirmed these findings.
ProtonVPN ranks at the top of 2026 security evaluations due to its combination of favorable jurisdiction, proven legal resistance track record, consecutive independent verification, and advanced security architecture. Redseclabs
NordVPN’s no-logs policy has been independently verified five times by Deloitte and PwC, most recently in late 2024, confirming that user activity and traffic data are not stored. Cybernews
The key standard today: first, read the audit date, not just the headline. Anything older than 24 months is stale. Next, check the scope — does the report examine server configurations and authentication flow, or just policy documents? Finally, look for RAM-only architecture, which enforces log impermanence at the hardware level. Redact
The question in 2026 is no longer “Does this VPN claim no-logs?” It is: “Can they prove it under legal, technical, and physical pressure?”
For businesses, that proof starts at the infrastructure level. Shop Jazz Cyber Shield’s full security lineup to build a network that doesn’t depend on trust — it depends on verified, enterprise-grade hardware.
🚩 7 Red Flags That Expose a Lying VPN
Before you subscribe to any VPN service, run through this checklist:
1. No Independent Third-Party Audit If firms like Cure53, Deloitte, PwC, or KPMG have never audited a VPN, the provider has not verified its no-log claim. Don’t rely on their word.
2. Headquarters in a 5-Eyes, 9-Eyes, or 14-Eyes Country Intelligence-sharing alliances between the US, UK, Canada, Australia, New Zealand, and partner nations can legally compel VPN providers to hand over data — and to stay silent about it.
3. Vague or Contradictory Privacy Policy Language If the homepage says “zero logs” but the privacy policy contains phrases like “we may collect data to improve services,” those two documents are in conflict. The fine print always wins in court.
4. No RAM-Only Server Architecture Traditional hard-drive servers retain data even after shutdown. RAM-only architecture enforces log impermanence at the hardware level Redact — meaning data is physically wiped on reboot with no way to recover it.
5. Free VPN Service With No Business Model Free VPNs may collect logs that identify users, and they can sell, share, or lose this data in a breach. CyberInsider If you are not paying for the product, your data is the product.
6. No Public Transparency Report Reputable providers publish regular reports detailing government data requests received and how they responded. No transparency report = no accountability.
7. Missing Kill Switch or DNS Leak Protection These are baseline privacy features. Any VPN serious about protecting users includes them. Their absence signals that privacy is not actually the priority.
Also read: Is Your Wi-Fi 6 Router Actually Safe? — essential settings every network administrator and home user should check right now.
❓ Frequently Asked Questions (FAQ)
A no-log policy means a VPN provider promises not to collect or store any records of your online activity — including your IP address, websites you visit, connection times, or bandwidth usage. However, PureVPN, IPVanish, HideMyAss, UFO VPN, and Hotspot Shield have shown that these providers often make this claim without having the infrastructure or intention to honor it.
Five VPNs have documented proof of deception. First, PureVPN logged data for the FBI. Then, IPVanish shared logs with the US government. Next, HideMyAss provided logs to UK and US law enforcement. Additionally, UFO VPN and six sister services exposed 1.2TB of logs on a public server, while Hotspot Shield faced an FTC complaint and suffered an IP leak.
ExpressVPN, ProtonVPN, and Mullvad have all had their no-log claims verified — either through multiple rounds of independent auditing or real-world events like law enforcement raids that found absolutely no user data to seize.
No. VPNs are a single software-layer tool and should never be the only line of defense. Businesses need hardware-level security: enterprise firewalls, managed network switches, and secure access points that enforce traffic policy at the infrastructure level.
RAM-only servers store all operational data in temporary memory rather than on physical hard drives. When the server reboots or is powered down, all data is permanently wiped. This means there is physically no log data to hand over to law enforcement — even under a court order.
Test your VPN for DNS leaks and IP leaks using dedicated test tools. If your real IP address or DNS server appears in the results while connected to the VPN, you have a leak regardless of what the VPN claims. This is exactly the type of vulnerability that exposed Hotspot Shield users.
With a properly functioning VPN and no leaks, your ISP sees encrypted tunnel traffic but not the content of your browsing. However, if your VPN has a DNS or IP leak — as Hotspot Shield did with CVE-2018-6460 — your real IP and activity can be exposed in real time. This is why network-level hardware security is essential alongside any VPN solution.
Look for: independent third-party audits completed within the last 12-24 months, RAM-only server infrastructure, jurisdiction outside 5/9/14-Eyes alliances, published transparency reports, and real-world legal cases where the provider successfully protected user data under pressure. Proof matters — promises do not.
Absolutely yes. A VPN encrypts your traffic in transit. A hardware firewall controls what traffic is allowed to enter or leave your network entirely — blocking threats before they ever reach your devices. These are complementary tools, not alternatives. Explore Fortinet, SonicWall, and WatchGuard firewalls for enterprise-grade protection.
✅ Final Verdict: Stop Trusting Promises. Start Verifying.
The five VPNs caught lying about their no-log policies all shared the same fatal flaw: they built their business model on a promise they could not — or would not — keep. When governments came calling, their no-log claims evaporated instantly.
In 2026, privacy is not a checkbox. It is an architecture.
For individuals: use a VPN that has passed independent audits and survived real-world legal pressure. For businesses and organizations: use hardware that enforces network-level policies to build security from the ground up, rather than relying on software that hackers can breach, courts can subpoena, or admins can misconfigure.
👉 Shop Enterprise Firewalls — Fortinet, SonicWall & WatchGuard 👉 Browse Managed Network Switches — Cisco, HPE Aruba & More 👉 Explore the Full Jazz Cyber Shield Security Store 👉 Read More Cybersecurity Guides on the Jazz Cyber Shield Blog



This really highlights the trust gap in the VPN industry. It’s a good reminder that users need to actively verify no-log claims instead of relying solely on marketing messages. Transparency and independent audits seem more important than ever for digital privacy.